
Cybersecurity
- • 100%thehackernews.com Cybercriminals Exploit HTTP Headers for Credential Theft via Large-Scale Phishing Attacks
Cybercriminals exploit HTTP header refresh techniques in phishing campaigns targeting corporations, government agencies, and schools for credential th

- • 98%arstechnica.com 1.3 million Android-based TV boxes backdoored; researchers still don’t know how
Infection corrals devices running AOSP-based firmware into a botnet.

> Infection corrals devices running AOSP-based firmware into a botnet.
- • 98%www.tomshardware.com North Korean hackers target Python devs with malware disguised as coding tests — hack has been underway for a year
Fake Python job opportunities used to attack programmers
> Fake Python job opportunities used to attack programmers
- • 100%thehackernews.com Apple Vision Pro Vulnerability Exposed Virtual Keyboard Inputs to Attackers
Apple patches Vision Pro vulnerability after GAZEploit attack exposes keystroke inference risk via gaze tracking.
- • 100%thehackernews.com New Linux Malware Campaign Exploits Oracle Weblogic to Mine Cryptocurrency
New Linux malware 'Hadooken' targets Oracle Weblogic, deploys crypto miners and DDoS botnet. Exploits vulnerabilities for lateral movement.

- • 96%www.wired.com Apple Vision Pro’s Eye Tracking Exposed What People Type
The Vision Pro uses 3D avatars on calls and for streaming. These researchers used eye tracking to work out the passwords and PINs people typed with their avatars.

> The Vision Pro uses 3D avatars on calls and for streaming. These researchers used eye tracking to work out the passwords and PINs people typed with their avatars.
Archived version: https://web.archive.org/web/20240912100207/https://www.wired.com/story/apple-vision-pro-persona-eye-tracking-spy-typing/
- thehackernews.com Beware: New Vo1d Malware Infects 1.3 Million Android TV Boxes Worldwide
Vo1d malware infects 1.3M Android TV boxes in 197 countries. Learn about this new backdoor threat and how it compromises device security.

- • 98%arstechnica.com Rogue WHOIS server gives researcher superpowers no one should ever have
.mobi top-level-domain managers changed the location of its WHOIS server. No one got the memo.

- • 100%arstechnica.com As quantum computing threats loom, Microsoft updates its core crypto library
Two algorithms added so far, two more planned in the coming months.

> Two algorithms added so far, two more planned in the coming months.
- • 100%www.darkreading.com Amateurish 'CosmicBeetle' Ransomware Stings Turkish SMBs
With an immature codebase and a "rather chaotic encryption scheme" prone to failure, the group targets small businesses with custom malware.

- • 95%thehackernews.com New RAMBO Attack Uses RAM Radio Signals to Steal Data from Air-Gapped Networks
New RAMBO attack exploits radio signals from RAM to steal data from air-gapped networks, posing cybersecurity risks.
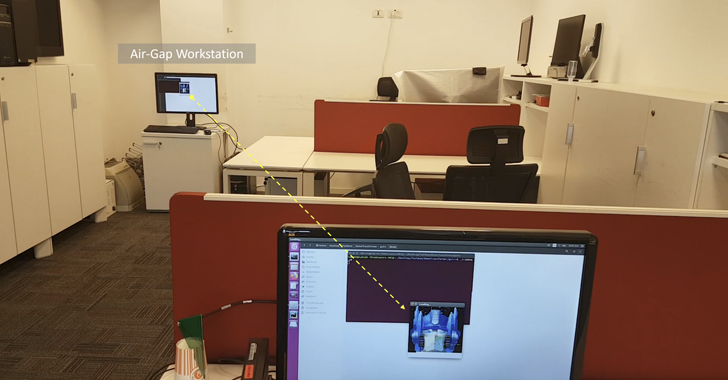
- • 96%thehackernews.com New PIXHELL Attack Exploits Screen Noise to Exfiltrates Data from Air-Gapped Computers
Discover PIXHELL, a new side-channel attack exploiting screen-generated noise to breach air-gapped computers and exfiltrate sensitive data.

> Microsoft Corp. today released updates to fix at least 79 security vulnerabilities in its Windows operating systems and related software, including multiple flaws that are already showing up in active attacks. Microsoft also corrected a critical bug that has caused some Windows 10 PCs to remain dangerously unpatched against actively exploited vulnerabilities for several months this year.
- • 100%www.darkreading.com Microsoft Discloses 4 Zero-Days in September Update
This month's Patch Tuesday contains a total of 79 vulnerabilities — the fourth largest of the year.

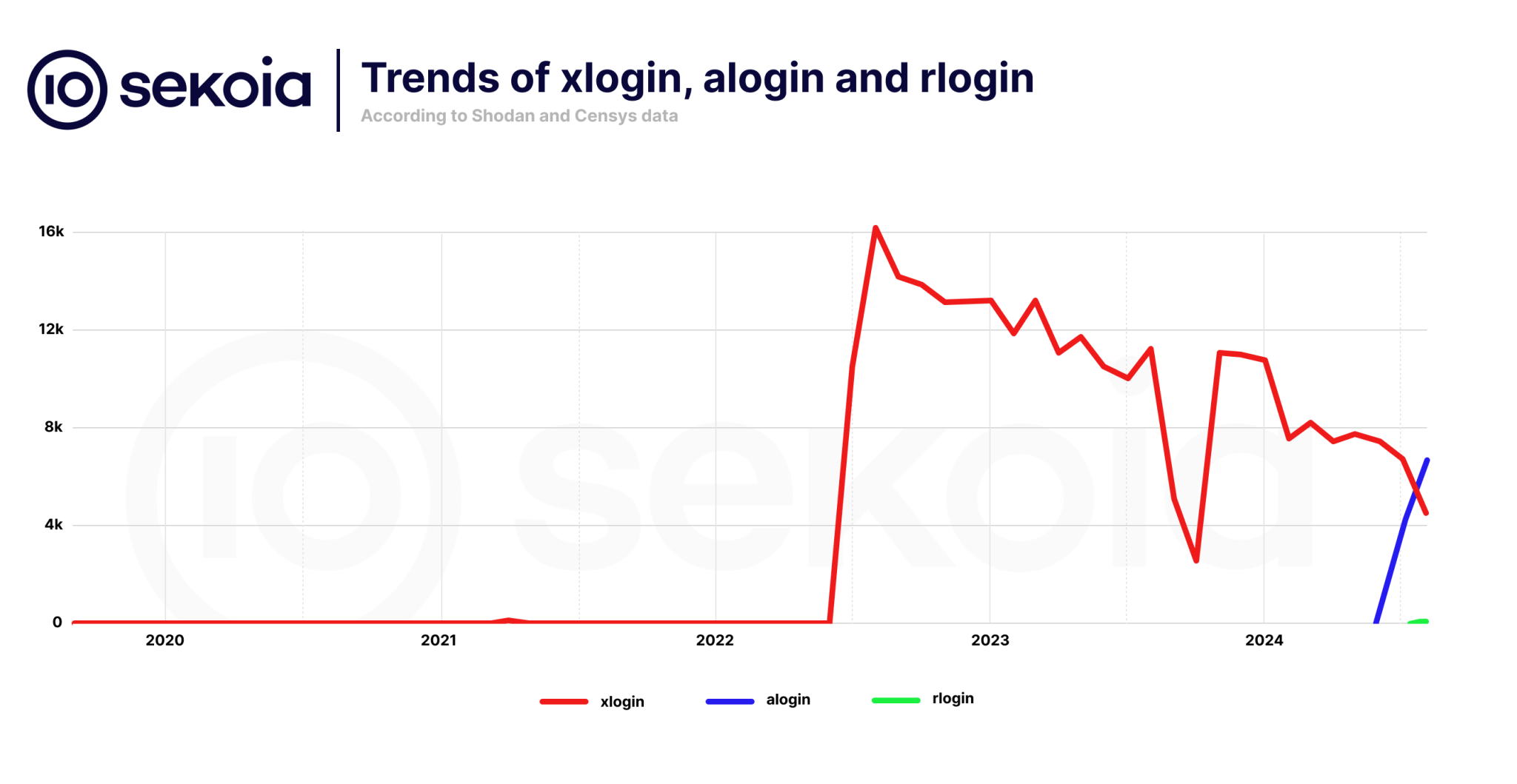
- • 100%securityaffairs.com Quad7 botnet evolves to more stealthy tactics to evade detection
The Quad7 botnet evolves and targets new SOHO devices, including Axentra media servers, Ruckus wireless routers and Zyxel VPN appliances.
- securityaffairs.com U.S. CISA adds SonicWall SonicOS, ImageMagick and Linux Kernel bugs to its Known Exploited Vulnerabilities catalog
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds SonicWall SonicOS, ImageMagick and Linux Kernel bugs to its Known Exploited Vulnerabilities catalog.

- • 100%www.darkreading.com 300K Victims Compromised in Avis Car Rental Breach
Though the company reports that data was exfiltrated in the breach, it has been remained tightlipped regarding the kind of data that was exposed.

- • 97%securityaffairs.com Poland thwarted cyberattacks that were carried out by Russia and Belarus
Polish security officials announced that they successfully thwarted cyberattacks that were carried out by Russia and Belarus.

- • 100%www.helpnetsecurity.com DockerSpy: Search for images on Docker Hub, extract sensitive information - Help Net Security
DockerSpy scans Docker Hub for images and retrieves sensitive information, including authentication secrets, private keys, and other data.
- • 100%thehackernews.com New Android SpyAgent Malware Uses OCR to Steal Crypto Wallet Recovery Keys
SpyAgent malware targets Android users, steals crypto wallet keys using OCR. Spreads via fake apps, evolves to use WebSockets. Expands from South Kore

- • 100%thehackernews.com Chinese Hackers Exploit Visual Studio Code in Southeast Asian Cyberattacks
Chinese hackers exploit Visual Studio Code in cyberattacks on Southeast Asian governments. New technique uses reverse shell for espionage and data the

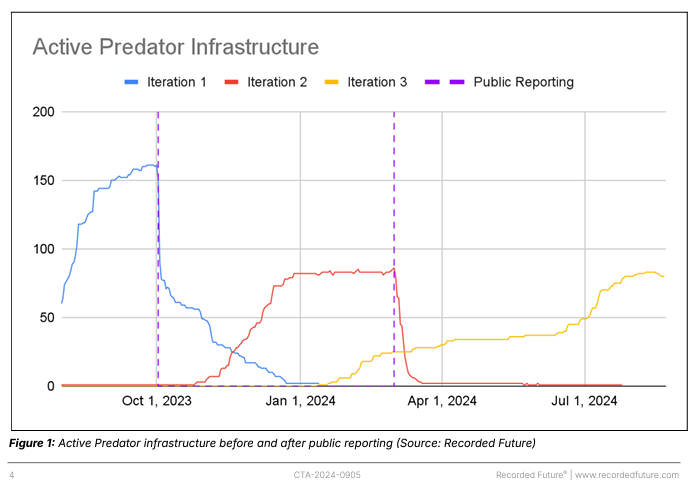
- • 100%securityaffairs.com Predator spyware operation is back with a new infrastructure
A new cluster of activity linked to Predator spyware using a new infrastructure was spotted following sanctions against Intellexa Consortium
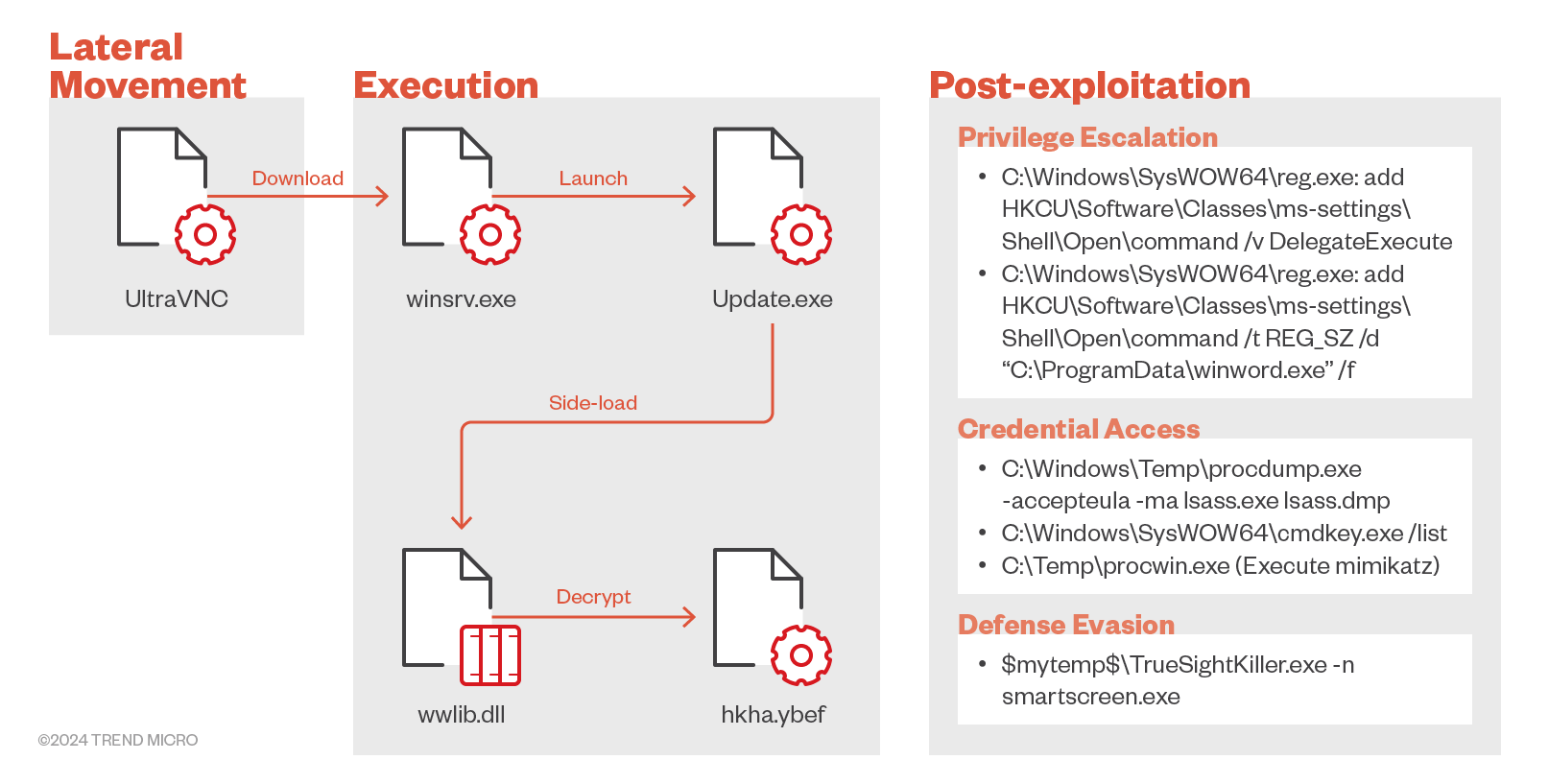
- • 100%securityaffairs.com TIDRONE APT targets drone manufacturers in Taiwan
A previously undocumented threat actor tracked TIDRONE targets organizations in military and satellite industries in Taiwan.
- www.darkreading.com Sovereign Tech Fund Invests in FreeBSD to Boost Security
The funds from Germany’s Sovereign Tech Fund will be used to integrate security features such as zero trust capabilities and tools for software bill of materials.

> The funds from Germany’s Sovereign Tech Fund will be used to integrate security features such as zero trust capabilities and tools for software bill of materials.
- • 98%arstechnica.com Found: 280 Android apps that use OCR to steal cryptocurrency credentials
Optical Character Recognition converts passwords shown in images to machine-readable text.

> Optical Character Recognition converts passwords shown in images to machine-readable text.
McAfee blog: https://www.mcafee.com/blogs/other-blogs/mcafee-labs/new-android-spyagent-campaign-steals-crypto-credentials-via-image-recognition/
- • 100%thehackernews.com Critical Security Flaw Found in LiteSpeed Cache Plugin for WordPress
WordPress LiteSpeed Cache plugin vulnerability could allow unauthenticated account takeover. Update now to fix the issue.

- • 91%www.darkreading.com Chinese 'Tropic Trooper' APT Targets Mideast Governments
In the past, the group has targeted different sectors in East and Southeast Asia, but recently has pivoted its focus to the Middle East, specifically to entities that publish human rights studies.

- • 100%arstechnica.com Zyxel warns of vulnerabilities in a wide range of its products
Most serious vulnerabilities carry severity ratings of 9.8 and 8.1 out of a possible 10.

> Most serious vulnerabilities carry severity ratings of 9.8 and 8.1 out of a possible 10.
