Infosec News
- www.microsoft.com Storm-0501: Ransomware attacks expanding to hybrid cloud environments | Microsoft Security Blog
Microsoft has observed the threat actor tracked as Storm-0501 launching a multi-staged attack where they compromised hybrid cloud environments and performed lateral movement from on-premises to cloud environment, leading to data exfiltration, credential theft, tampering, persistent backdoor access, ...

- www.elastic.co Betting on Bots: Investigating Linux malware, crypto mining, and gambling API abuse — Elastic Security Labs
The REF6138 campaign involved cryptomining, DDoS attacks, and potential money laundering via gambling APIs, highlighting the attackers' use of evolving malware and stealthy communication channels.

- cloud.google.com Staying a Step Ahead: Mitigating the DPRK IT Worker Threat | Google Cloud Blog
North Korea's IT workforce presents a persistent and escalating cyber threat.

- • 100%therecord.media Insurance giant Globe Life facing extortion attempts after data theft from subsidiary
The company told regulators at the U.S. Securities and Exchange Commission (SEC) that it reported the incident — which involves a variety of sensitive data on about 5,000 people — to federal law enforcement.
- • 100%unit42.paloaltonetworks.com Lynx Ransomware: A Rebranding of INC Ransomware
Discover recent attacks using Lynx ransomware, a rebrand of INC, targeting multiple crucial sectors in the U.S. and UK with prevalent double-extortion tactics. Discover recent attacks using Lynx ransomware, a rebrand of INC, targeting multiple crucial sectors in the U.S. and UK with prevalent double...
- • 100%news.sophos.com From QR to compromise: The growing “quishing” threat
Attackers leverage QR codes in PDF email attachments to spearphish corporate credentials from mobile devices
- securelist.com Cyberthreats in the Middle East H1 2024
The Kaspersky Digital Footprint Intelligence team shares insights into the H1 2024 Middle Eastern cyberthreat landscape: hacktivism, initial access brokers, ransomware, stealers, and so on.

- • 100%thehackernews.com Microsoft Reveals macOS Vulnerability that Bypasses Privacy Controls in Safari Browser
Microsoft uncovers a macOS flaw allowing unauthorized access to sensitive data. Update your device now!

- thecyberexpress.com Kubernetes Image Builder Vulnerability: CVE-2024-9486 Risk
The Kubernetes Image Builder vulnerability (CVE-2024-9486) poses a critical security threat.

- haveibeenpwned.com Have I Been Pwned: Pwned websites
Have I Been Pwned allows you to search across multiple data breaches to see if your email address or phone number has been compromised.
- blogs.microsoft.com Escalating Cyber Threats Demand Stronger Global Defense and Cooperation
Discover the alarming rise in cyber threats, with attacks on Microsoft customers doubling to 600 million per day. The latest Microsoft Digital Defense Report reveals the increasing collusion between nation-state actors and cybercriminals, highlighting the global impact on geopolitical conflicts and ...

- • 75%www.trendmicro.com How to Mitigate the Impact of Rogue AI Risks
This is the fifth blog post in an ongoing series on Rogue AI about mitigating AI risks. Keep following for more technical guidance, case studies, and insights

- • 100%therecord.media More than 5,000 arrested, thousands of websites disrupted in crackdown on illegal gambling during Euro tournament
Authorities in 28 countries orchestrated thousands of arrests and website shutdowns while also disrupting scam centers and their related human trafficking and money laundering operations.

- cloud.google.com LummaC2: Obfuscation Through Indirect Control Flow | Google Cloud Blog
Analysis of malware samples using a technique to thwart all binary analysis tools, and hinder reverse engineering efforts.

- • 66%www.trustwave.com What We Know So Far About Zero-Day CUPS Vulnerabilities: CVE-2024-47176, CVE-2024-47076, CVE-2024-47175, and CVE-2024-47177
On September 26, 2024, security researcher Simone Margaritelli disclosed the details of four OpenPrinting Common UNIX Printing System (CUPS) vulnerabilities.
- • 66%www.group-ib.com Cybersecurity Services, Solutions & Products. Global Provider | Group-IB
Leading provider of cybersecurity solutions: Threat Intelligence, antifraud, anti-APT. Protect better, respond faster to network security attacks and threats.

- www.elastic.co Cups Overflow: When your printer spills more than Ink — Elastic Security Labs
Elastic Security Labs discusses detection and mitigation strategies for vulnerabilities in the CUPS printing system, which allow unauthenticated attackers to exploit the system via IPP and mDNS, resulting in remote code execution (RCE) on UNIX-based systems such as Linux, macOS, BSDs, ChromeOS, and ...

- • 100%thehackernews.com Researchers Uncover Cicada3301 Ransomware Operations and Its Affiliate Program
Group-IB reveals Cicada3301 ransomware’s affiliate panel, targeting U.S. and U.K. sectors with cross-platform attacks.

- haveibeenpwned.com Have I Been Pwned: Pwned websites
Have I Been Pwned allows you to search across multiple data breaches to see if your email address or phone number has been compromised.
- thecyberexpress.com Globe Life Faces Extortion After Hackers Steal Customer Data
American insurance giant Globe Life is facing extortion demands from hackers who stole data on over 5,000 individuals from one of its subsidiaries.

- securelist.com SideWinder APT’s post-exploitation framework analysis
Kaspersky analyzes SideWinder APT’s recent activity: new targets in the MiddleEast and Africa, post-exploitation tools and techniques.

- www.microsoft.com Microsoft's guidance to help mitigate Kerberoasting | Microsoft Security Blog
Kerberoasting, a well-known Active Directory (AD) attack vector, enables threat actors to steal credentials and navigate through devices and networks. Microsoft is sharing recommended actions administrators can take now to help prevent successful Kerberoasting cyberattacks.

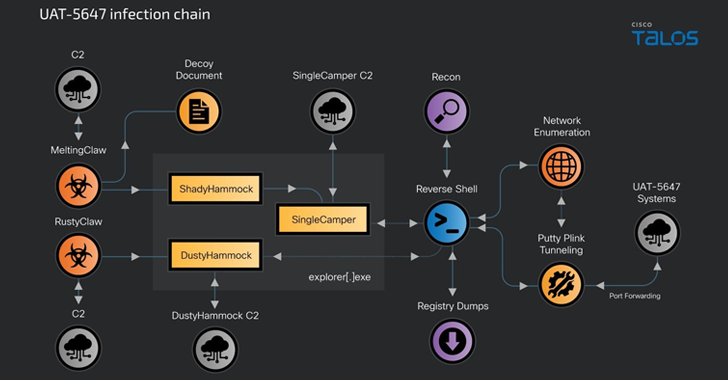
- • 100%thehackernews.com Russian RomCom Attacks Target Ukrainian Government with New SingleCamper RAT Variant
RomCom cyber attacks target Ukraine with new SingleCamper RAT, aiming for espionage and ransomware.
- • 100%therecord.media Alabama man arrested in breach of SEC social media account
The Justice Department said a 25-year-old Athens, Alabama, man used a SIM swap to break into the Securities and Exchange Commission's account on X to post false information about a bitcoin-related security.

- • 50%unit42.paloaltonetworks.com Unit 42 Looks Toward the Threat Frontier: Preparing for Emerging AI Risks
The Unit 42 Threat Frontier report discusses GenAI's impact on cybersecurity, emphasizing the need for AI-specific defenses and proactive security. The Unit 42 Threat Frontier report discusses GenAI's impact on cybersecurity, emphasizing the need for AI-specific defenses and proactive security.

- www.elastic.co Elevate Your Threat Hunting with Elastic — Elastic Security Labs
Elastic is releasing a threat hunting package designed to aid defenders with proactive detection queries to identify actor-agnostic intrusions.

- www.trendmicro.com 5 Forrester Takeaways Around AI Security
Learn five Forrester AI security takeaways.

- • 100%www.trustwave.com Feline Hackers Among Us? (A Deep Dive and Simulation of the Meow Attack)
Attackers are on the prowl for weaknesses in infrastructure and software like a cat eyeing its helpless prey.
- cloud.google.com capa Explorer Web: A Web-Based Tool for Program Capability Analysis | Google Cloud Blog
capa Explorer Web is a browser-based tool to display the capabilities found by capa, our popular reverse engineering tool.
