
Pulse of Truth
Temu denies it was hacked or suffered a data breach after a threat actor claimed to be selling a stolen database containing 87 million records of customer information. [...]
- www.darkreading.com Thousands of ServiceNow KB Instances Expose Corporate Data
Despite security updates to protect data, 45% of total enterprise instances of the cloud-based IT management platform leaked PII, internal system details, and active credentials over the past year.

Despite security updates to protect data, 45% of total enterprise instances of the cloud-based IT management platform leaked PII, internal system details, and active credentials over the past year.
- restoreprivacy.com Discord Introduces New End-to-End Encryption Protocol ‘DAVE’
Discord has introduced DAVE, its new end-to-end encryption (E2EE) protocol for audio and video communications on the platform.

Discord has introduced DAVE, its new end-to-end encryption (E2EE) protocol for audio and video communications, aimed at enhancing user privacy across voice calls, group DMs, and Go Live streams. This major security upgrade marks a significant step in Discord’s ongoing efforts to protect the 200 million monthly users on its platform. Announced by one of … The post Discord Introduces New End-to-End Encryption Protocol ‘DAVE’ appeared first on RestorePrivacy.
- arstechnica.com Massive China-state IoT botnet went undetected for four years—until now
75% of infected devices were located in homes and offices in North America and Europe.

75% of infected devices were located in homes and offices in North America and Europe.
- go.theregister.com WhatsApp View Once flaw fix lasts days before failing
View Forever, more like it, as Meta's privacy feature again revealed to be futile with a little light hacking

View Forever, more like it, as Meta's privacy feature again revealed to be futile with a little light hacking A fix deployed by Meta to stop people repeatedly viewing WhatsApp’s so-called View Once messages – photos, videos, and voice recordings that disappear from chats after a recipient sees them – has been defeated in less than a week by white-hat hackers.…
- www.techmeme.com Australian police say they infiltrated Ghost, a global encrypted communications app developed for criminals, arresting dozens, including the app's alleged admin
By Rod McGuirk / Associated Press. View the full context on Techmeme.
Rod McGuirk / Associated Press: Australian police say they infiltrated Ghost, a global encrypted communications app developed for criminals, arresting dozens, including the app's alleged admin — Australian police said Wednesday they have infiltrated Ghost, an encrypted global communications app developed for criminals, leading to dozens of arrests.
- arstechnica.com US can’t ban TikTok for security reasons while ignoring Temu, other apps
TikTok's survival in the US may depend on an appeals court ruling this December.

TikTok's survival in the US may depend on an appeals court ruling this December.
- www.techmeme.com Pew survey: 17% of US adults say they regularly get news on TikTok in 2024, up from 14% in 2023 and 3% in 2020; 39% aged 18 to 29 do so, up from 32% a year ago
By Alicia Clanton / Bloomberg. View the full context on Techmeme.

Alicia Clanton / Bloomberg: Pew survey: 17% of US adults say they regularly get news on TikTok in 2024, up from 14% in 2023 and 3% in 2020; 39% aged 18 to 29 do so, up from 32% a year ago — - Almost 40% of young adults regularly get news from the app — TikTok faces a ban in the US if parent company doesn't divest
- go.theregister.com Chinese boffins claim Starlink signals can defeat stealth
If this really was that useful, they wouldn't be telling us

If this really was that useful, they wouldn't be telling us According to a Chinese state-sanctioned study, signals from SpaceX Starlink broadband internet satellites could be used to track US stealth fighters, such as the F-22.…
Ransomware gangs like BianLian and Rhysida increasingly use Microsoft's Azure Storage Explorer and AzCopy to steal data from breached networks and store it in Azure Blob storage. [...]
- go.theregister.com DoJ accuses Chinese national of phishing for military code
May have reeled in blueprints related to weapons development

May have reeled in blueprints related to weapons development A Chinese national has been accused of conducting a years-long spear-phishing campaign that aimed to steal source code from the US Army and NASA, plus other highly sensitive software used in aerospace engineering and military applications.…
- www.darkreading.com 'Marko Polo' Creates Globe-Spanning Cybercrime Juggernaut
The Eastern European group is actively expanding its financial fraud activities, with its pipelines representing a veritable Silk Road for the transfer of cryptocurrency, and lucrative and exploitable data.
The Eastern European group is actively expanding its financial fraud activities, with its pipelines representing a veritable Silk Road for the transfer of cryptocurrency, and lucrative and exploitable data.
- go.theregister.com 23andMe settles class-action breach lawsuit for $30 million
Also: Apple to end NSO Group lawsuit; Malicious Python dev job offers; Dark web kingpins busted; and more

Also: Apple to end NSO Group lawsuit; Malicious Python dev job offers; Dark web kingpins busted; and more Infosec In Brief Genetic testing outfit 23andMe has settled a proposed class action case related to a 2023 data breach for $30 million.…
- www.techmeme.com Apple's Activation Lock for iPhone components will make a huge dent in the market for stolen iPhones, though it introduces another barrier to DIY repairs
By Ben Lovejoy / 9to5Mac. View the full context on Techmeme.

Ben Lovejoy / 9to5Mac: Apple's Activation Lock for iPhone components will make a huge dent in the market for stolen iPhones, though it introduces another barrier to DIY repairs — Apple's latest theft-prevention measure went live for beta testers yesterday: Activation Lock for iPhone components.
- www.helpnetsecurity.com Beyond human IAM: The rising tide of machine identities - Help Net Security
The complexity of machine identity management is compounded by the lack of a “single pane of glass” solution.

Remember when managing user accounts was your biggest headache? Those were simpler times. Today, we’re drowning in a sea of machine identities, and it’s time to learn how to swim – or risk going under. In the ever-expanding universe of hybrid and multicloud environments, machine identities have proliferated faster than cat videos on the Internet. According to CyberArk, these non-human entities—think workloads, services, and anything else that goes ‘beep’ in the night—now outnumber human identities … More → The post Beyond human IAM: The rising tide of machine identities appeared first on Help Net Security.
A Twitter account known as DarkWebInformer has claimed that a notorious hacker, identified only by the alias “888,” has allegedly leaked sensitive data belonging to SAP employees. A member of BreachForums has claimed responsibility for leaking an employee database purportedly belonging to SAP SE, one of the world’s leading enterprise software companies. The leak reportedly […] The post Threat Actor 888 Allegedly Claims Leak of SAP Employees Data appeared first on Cyber Security News.
- www.techspot.com Study suggests SEC visits may be tipping off insiders, leading to stock sell-offs
New research around stock behavior led by professors from universities across the Midwest took a novel approach. The academics used commercially available mobile phone location data to...

New research around stock behavior led by professors from universities across the Midwest took a novel approach. The academics used commercially available mobile phone location data to track devices spending significant time around SEC offices. They then traced those devices traveling to corporate headquarters in the year before the Covid...Read Entire Article
Transport for London (TfL) says that all staff (roughly 30,000 employees) must attend in-person appointments to verify their identities and reset passwords following a cybersecurity incident disclosed almost two weeks ago. [...]
- thehackernews.com Ireland's Watchdog Launches Inquiry into Google's AI Data Practices in Europe
Irish Data Protection Commission launches inquiry into Google's AI model PaLM 2, investigating GDPR compliance in personal data processing for AI dev

The Irish Data Protection Commission (DPC) has announced that it has commenced a "Cross-Border statutory inquiry" into Google's foundational artificial intelligence (AI) model to determine whether the tech giant has adhered to data protection regulations in the region when processing the personal data of European users. "The statutory inquiry concerns the question of whether Google has complied
- go.theregister.com More details on that Windows Installer 'make me admin' hole
What kind of OS can be hijacked by clicking a link at just the right time? Microsoft's

What kind of OS can be hijacked by clicking a link at just the right time? Microsoft's In this week's Patch Tuesday Microsoft alerted users to, among other vulnerabilities, a flaw in Windows Installer that can be exploited by malware or a rogue user to gain SYSTEM-level privileges to hijack a PC.…
- go.theregister.com Some Fortinet customer data stolen from cloud storage
That would explain this 440GB leak, then
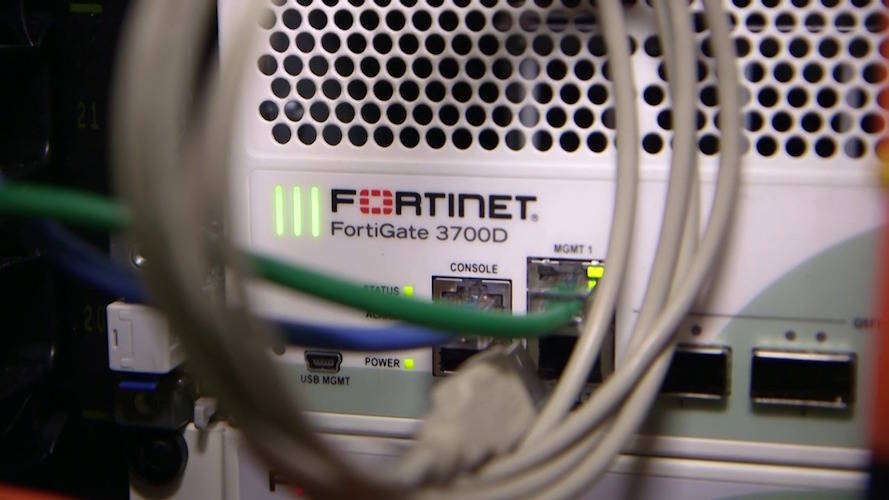
That would explain this 440GB leak, then Fortinet has admitted that bad actors accessed cloud-hosted data about its customers, but insisted it was a "limited number" of files. The question is: how limited is "limited"?…
Threat actors have infected over 1.3 million TV streaming boxes running Android with a new Vo1d backdoor malware, allowing the attackers to take full control of the devices. [...]
- www.wired.com Apple Vision Pro’s Eye Tracking Exposed What People Type
The Vision Pro uses 3D avatars on calls and for streaming. These researchers used eye tracking to work out the passwords and PINs people typed with their avatars.

The Vision Pro uses 3D avatars on calls and for streaming. These researchers used eye tracking to work out the passwords and PINs people typed with their avatars.
- www.helpnetsecurity.com Losses due to cryptocurrency and BEC scams are soaring - Help Net Security
2023 was a particularly devastating year for victims of cryptocurrency and business email compromise (BEC) scams.

Every type of fraud is on the rise, and 2023 was a particularly devastating year for victims of cryptocurrency and business email compromise (BEC) scams, according to the FBI. Cryptocurrency fraud Based on complaints filed to FBI’s Internet Crime Complaint Center (IC3) in 2023, the year saw over $5.6 billion in losses tied to cryptocurrency fraud alone, marking a dramatic 45% increase over 2022 figures. Criminals are exploiting the difficulties of tracing and recovering cryptocurrency … More → The post Losses due to cryptocurrency and BEC scams are soaring appeared first on Help Net Security.
- go.theregister.com Cyber-crook leaks 20GB of data 'stolen' from Capgemini
Allegedly pilfered database has source code, private keys, staff info, T-Mobile VM logs, more

Allegedly pilfered database has source code, private keys, staff info, T-Mobile VM logs, more A miscreant claims to have broken into Capgemini and leaked a large amount of sensitive data stolen from the technology services giant – including source code, credentials, and T-Mobile's virtual machine logs.…
- arstechnica.com As quantum computing threats loom, Microsoft updates its core crypto library
Two algorithms added so far, two more planned in the coming months.

Two algorithms added so far, two more planned in the coming months.
- www.bloomberg.com Mastercard Agrees to Buy Cyber-Defense Firm for $2.65 Billion
Mastercard Inc. agreed to buy cyber-defense firm Recorded Future for $2.65 billion to boost its ability to protect the card company’s massive global-payments system.
Mastercard Inc. agreed to buy cyber-defense firm Recorded Future for $2.65 billion to boost its ability to protect the card company’s massive global-payments system.
- www.hackerone.com The Rise of Bug Bounty Programs in S-1 Filings: A New Standard in Corporate Security
Learn why more organizations are including their bug bounty programs in S-1 filings and other corporate disclosures.

Learn why more organizations are including their bug bounty programs in S-1 filings and other corporate disclosures.
A cybersecurity researcher is urging users to upgrade Adobe Acrobat Reader after a fix was released yesterday for a remote code execution zero-day with a public in-the-wild proof-of-concept exploit. [...]
Members of the North Korean hacker group Lazarus posing as recruiters are baiting Python developers with coding test project for password management products that include malware. [...]
- labs.watchtowr.com We Spent $20 To Achieve RCE And Accidentally Became The Admins Of .MOBI
Welcome back to another watchTowr Labs blog. Brace yourselves, this is one of our most astounding discoveries. Summary What started out as a bit of fun between colleagues while avoiding the Vegas heat and $20 bottles of water in our Black Hat hotel rooms - has now seemingly become a
Comments
Six Chinese nationals and a Singaporean have been arrested on Monday in Singapore for their alleged role in malicious cyber activities committed in connection with a "global syndicate." [...]
- go.theregister.com You paid the ransom, and now the decryptor doesn't work
A really big oh sh*t moment, for sure

A really big oh sh*t moment, for sure For C-suite execs and security leaders, discovering your organization has been breached, your critical systems locked up and your data stolen, then receiving a ransom demand, is probably the worst day of your professional life.…
- go.theregister.com India to train 5000 ‘Cyber Commandos’
Minister reckons dedicated cops necessary to protect digital transactions

Minister reckons dedicated cops necessary to protect digital transactions India has announced a plan to train a specialized wing of 5000 "Cyber Commandos" in the next five years, as part of its efforts to address cyber crime.…
- https:// packetstormsecurity.com /files/181434/proxmark3-4.18994.tar.gz
This is a custom firmware written for the Proxmark3 device. It extends the currently available firmware. This release is nicknamed "Backdoor".
The RansomHub ransomware gang has been using TDSSKiller, a legitimate tool from Kaspersky, to disable endpoint detection and response (EDR) services on target systems. [...]
Ivanti has fixed a maximum severity vulnerability in its Endpoint Management software (EPM) that can let unauthenticated attackers gain remote code execution on the core server. [...]
- www.helpnetsecurity.com Microsoft fixes 4 exploited zero-days and a code defect that nixed earlier security fixes - Help Net Security
Microsoft fixes exploited 0-days (CVE-2024-38217, CVE-2024-38226, CVE-2024-38014, CVE-2024-43461) and a serious code defect (CVE-2024-43491).
September 2024 Patch Tuesday is here and Microsoft has delivered 79 fixes, including those for a handful of zero-days (CVE-2024-38217, CVE-2024-38226, CVE-2024-38014, CVE-2024-43461) exploited by attackers in the wild, and a Windows 10 code defect (CVE-2024-43491) that rolled back earlier CVE fixes. The actively exploited flaws Let’s start with the only one that was previously publicly known: CVE-2024-38217, a vulnerability that allows attackers to bypass Mark of the Web (MotW). Elastic Security researcher Joe Desimone … More → The post Microsoft fixes 4 exploited zero-days and a code defect that nixed earlier security fixes appeared first on Help Net Security.
- gizmodo.com Ford Seeks Patent for Software That Records Your Conversations to Serve You Ads
Would you want to drive a truck that was constantly listening to you?

Would you want to drive a truck that was constantly listening to you?