Security

We released version 1.5.0 of the Vulnerability Lookup project! 🎉 (https://github.com/cve-search/vulnerability-lookup/)
!edit-comments-with-tags !meta-field !Japanese source
This update brings significant new features, improvements, and fixes.
🆕 Notable Changes
We've integrated the Japan Database of Vulnerability Countermeasure Information (JVN DB), correlating security advisories from multiple sources (including NVD, GitHub, and CSAF, etc.) already available in Vulnerability Lookup.
You can now assign tags to comments directly on the website. These tags are stored in the comment's meta field and utilize the MISP Project taxonomy for vulnerabilities. Explore the taxonomy here.
We've enhanced the API to allow users to filter comments and bundles based on data available in the meta JSON field of the objects. This paves the way for leveraging more taxonomies in the future.
More details in the release notes.
Thank you very much to all the contributors and testers! 🙏
As always, feel free to create an account on the main instance operated by CIRCL.
We eagerly await your contributions! 😊
- • 100%wihkum.com Wihkum - Emergency Response App for Schools in 2024
Wihkum provides mobile safety solutions for schools. Our crisis management software ensures student safety. Request a free demo!
Teacher assaults in schools are a growing concern, impacting both staff safety and the learning environment. These incidents can range from verbal confrontations to physical altercations, making it crucial for schools to have effective safety measures in place. One of the most effective tools to ensure a swift and coordinated response is an emergency response app.
Wihkum, a cutting-edge emergency response app designed specifically for schools, offers a robust solution to this pressing issue. With its features including instant alerts, real-time communication with emergency services, and location tracking, Wihkum helps schools respond promptly to incidents of teacher assault and other emergencies. By integrating Wihkum into your school's safety protocol, you can enhance the security of your staff and create a safer learning environment for students.
Explore how Wihkum can be a vital component in your school's emergency preparedness strategy and contribute to a safer school environment.
- iverify.io iVerify Discovers Android Vulnerability Impacting Millions of Pixel Devices Around the World
iVerify discovered an Android package, "Showcase.apk," with excessive system privileges, including remote code execution and remote package installation capabilities, on a very large percentage of Pixel devices shipped worldwide since September 2017.
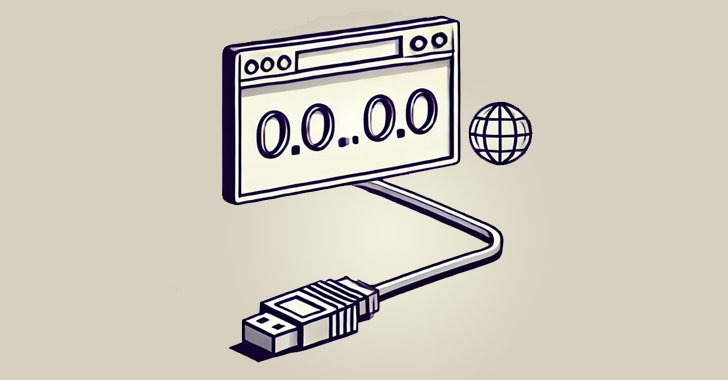
- • 88%thehackernews.com 0.0.0.0 Day: 18-Year-Old Browser Vulnerability Impacts MacOS and Linux Devices
Critical 0.0.0.0 Day browser vulnerability discovered, impacting Chrome, Firefox, Safari. Exploits local networks on MacOS and Linux
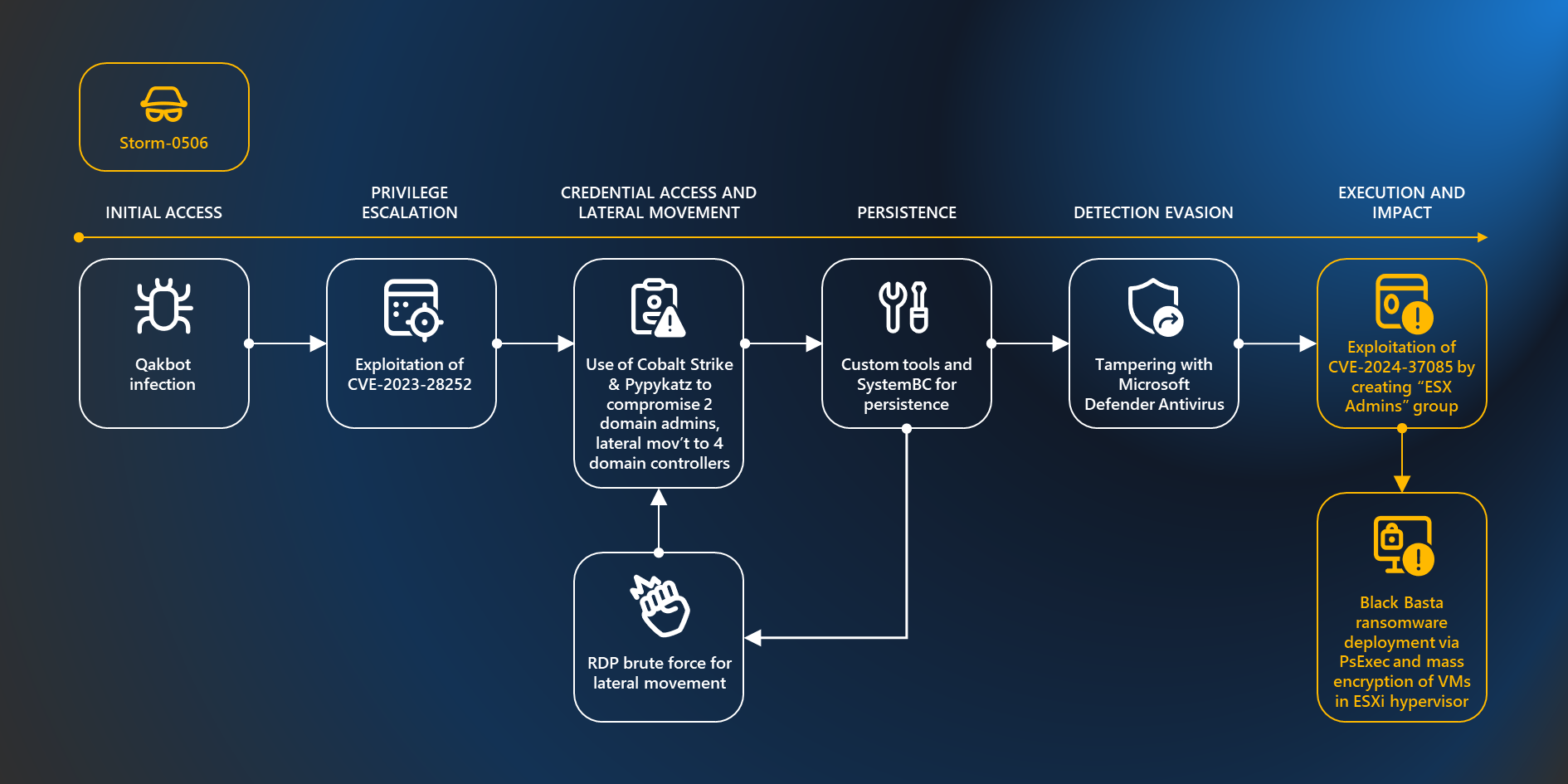
- www.microsoft.com Ransomware operators exploit ESXi hypervisor vulnerability for mass encryption | Microsoft Security Blog
Microsoft Security researchers have observed a vulnerability used by various ransomware operators to get full administrative access to domain-joined ESXi hypervisors and encrypt the virtual machines running on them. The vulnerability involves creating a group called “ESX Admins” in Active Directory ...
- • 71%www.bleepingcomputer.com Signal downplays encryption key flaw, fixes it after X drama
Signal is finally tightening its desktop client's security by changing how it stores plain text encryption keys for the data store after downplaying the issue since 2018.

- github.com GitHub - cve-search/vulnerability-lookup: Vulnerability Lookup facilitates quick correlation of vulnerabilities from various sources, independent of vulnerability IDs, and streamlines the management of Coordinated Vulnerability Disclosure (CVD).
Vulnerability Lookup facilitates quick correlation of vulnerabilities from various sources, independent of vulnerability IDs, and streamlines the management of Coordinated Vulnerability Disclosure ...
cross-posted from: https://lemmy.ml/post/18049618
> Vulnerability Lookup facilitates quick correlation of vulnerabilities from various sources (NIST, GitHub, CSAF-Siemens, CSAF-CISCO, CSAF-CERT-Bund, PySec, VARIoT, etc.), > independent of vulnerability IDs, and streamlines the management of Coordinated Vulnerability Disclosure (CVD). > Vulnerability Lookup is also a collaborative platform where users can comment on security advisories and create bundles. > > A Vulnerability Lookup instance operated by CIRCL > is available at https://vulnerability.circl.lu.
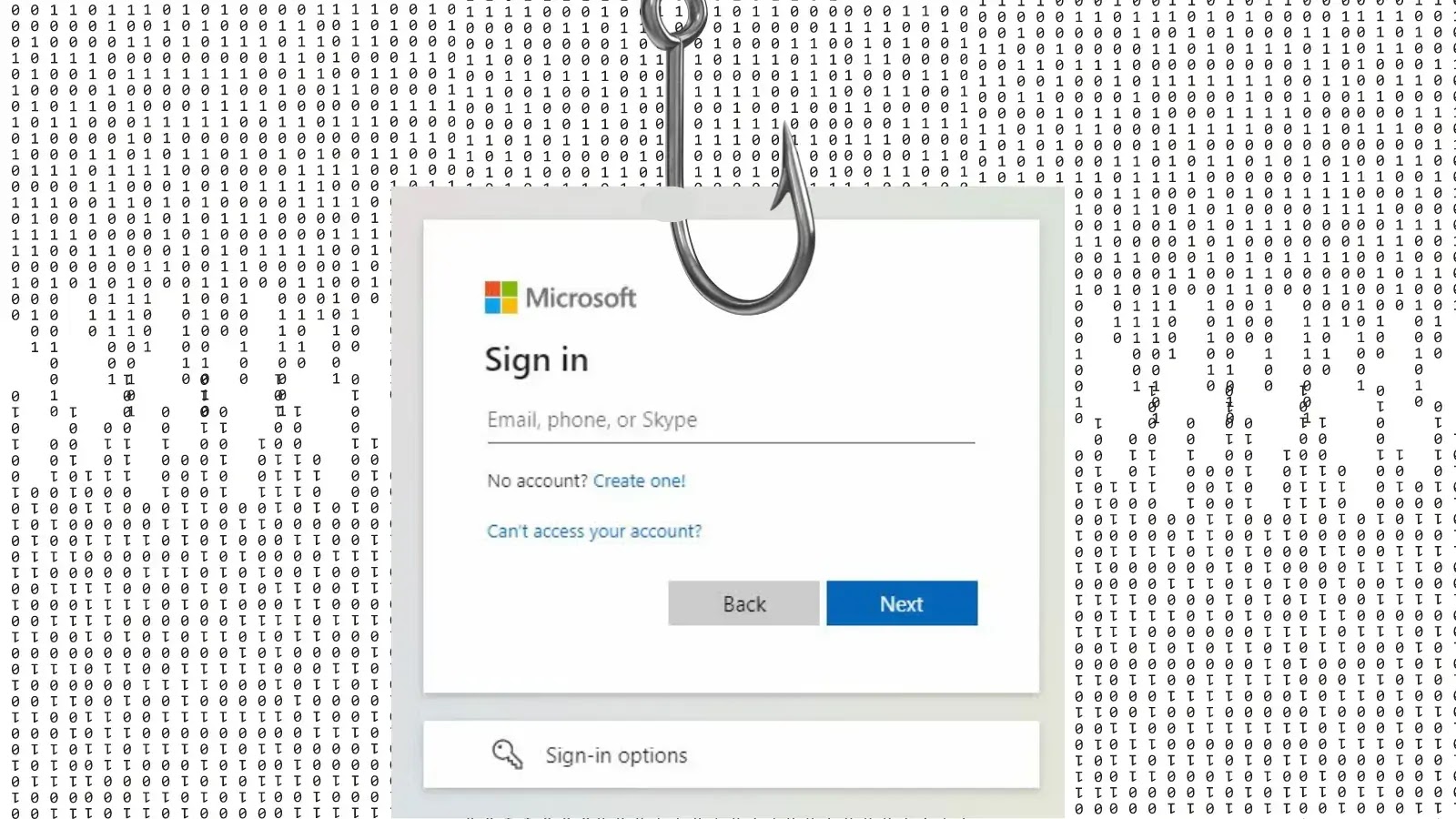
Reposted from: https://lemmings.world/post/10865023
> 1. Recognize the common signs > > • Urgent or emotionally appealing language > • Requests to send personal or financial information > • Unexpected attachments > • Untrusted shortened URLs > • Email addresses that do not match the supposed sender > • Poor writing/misspellings (less common) > > 2. Resist and report > Report suspicious messages by using the “report spam” feature. > If the message is designed to resemble an organization you trust, report the message by alerting the organization using their contact information found on their webpage. > > I have found also these phishing reporting pages: > > SITE: https://safebrowsing.google.com/safebrowsing/report_phish/ > > SITE: https://www.ncsc.gov.uk/section/about-this-website/report-scam-website > > SITE: https://www.scamwatcher.com/scam/add?type=fraudulent_website > > SITE/EMAIL: https://report.netcraft.com/report ( scam [\AT\] netcraft [\D0T\] com - for a phishing/fraud mail forwarding ) > > EMAIL: https://www.ncsc.gov.uk/collection/phishing-scams/report-scam-email#section_1 - forward phish mail to report [\AT\] phishing [\D0T\] gov [\D0T\] uk > > EMAIL: https://apwg.org/reportphishing/ ( reportphishing [\AT\] apwg [\D0T\] org - forward phishing mail as attachment if possible ) > > EMAIL: phishing-report [\AT\] us-cert [\D0T\] gov (phishing message should be sent as attachment possibly or its full source code in a message BODY.) > > OTHER: https://www.knowbe4.com/free-phish-alert (email client extension) > > feedback or new additions are welcome > > 3. Delete > Delete the message. Don’t reply or click on any attachment or link, including any “unsubscribe” link. > The unsubscribe button could also carry a link used for phishing. Just delete > > _________________________________________________ > > Source: https://www.cisa.gov/secure-our-world/recognize-and-report-phishing > > Send this to your friends, especially internet beginners.
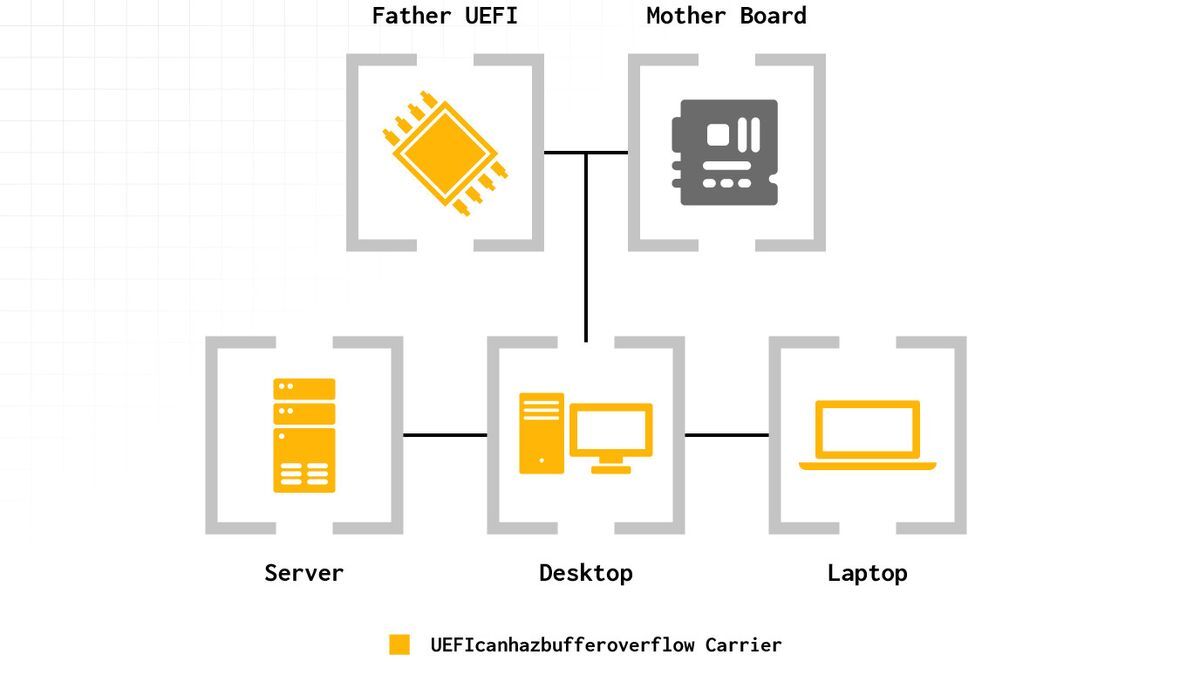
- • 100%www.tomshardware.com Firmware flaw affects numerous generations of Intel CPUs — UEFI code execution vulnerability found for Intel CPUs from 14th Gen Raptor Lake to 6th Gen Skylake CPUs, and TPM will not save you
Eclypsium Automata uncovers Phoenix as the latest to fall to a significant Arbitrary Code Execution exploit impacting Lenovo, AMI, Insyde, and Intel motherboard firmware.
- • 85%www.forbes.com New Wi-Fi Takeover Attack—All Windows Users Warned To Update Now
Microsoft has released a critical security update for users of all supported Windows versions as a new Wi-Fi compromise requiring no authentication has been confirmed.

- www.buskill.in BusKill Canary #8 - BusKill
This post contains the cryptographically-signed BusKill warrant canary #008 for June 2024 to January 2025.

This post contains a canary message that's cryptographically signed by the official BusKill PGP release key
| [!BusKill Canary #008](https://www.buskill.in/canary-008/) | |:--:| | The BusKill project just published their Warrant Canary #008 |
For more information about BusKill canaries, see:
- <https://buskill.in/canary>
``` -----BEGIN PGP SIGNED MESSAGE----- Hash: SHA512
Status: All good Release: 2024-06-11 Period: 2024-06-01 to 2024-12-31 Expiry: 2025-01-31
Statements ==========
The BusKill Team who have digitally signed this file [1] state the following:
-
The date of issue of this canary is June 11, 2024.
-
The current BusKill Signing Key (2020.07) is
E0AF FF57 DC00 FBE0 5635 8761 4AE2 1E19 36CE 786A
-
We positively confirm, to the best of our knowledge, that the integrity of our systems are sound: all our infrastructure is in our control, we have not been compromised or suffered a data breach, we have not disclosed any private keys, we have not introduced any backdoors, and we have not been forced to modify our system to allow access or information leakage to a third party in any way.
-
We plan to publish the next of these canary statements before the Expiry date listed above. Special note should be taken if no new canary is published by that time or if the list of statements changes without plausible explanation.
Special announcements =====================
None.
Disclaimers and notes =====================
This canary scheme is not infallible. Although signing the declaration makes it very difficult for a third party to produce arbitrary declarations, it does not prevent them from using force or other means, like blackmail or compromising the signers' laptops, to coerce us to produce false declarations.
The news feeds quoted below (Proof of freshness) serves to demonstrate that this canary could not have been created prior to the date stated. It shows that a series of canaries was not created in advance.
This declaration is merely a best effort and is provided without any guarantee or warranty. It is not legally binding in any way to anybody. None of the signers should be ever held legally responsible for any of the statements made here.
Proof of freshness ==================
04 Jun 24 14:10:16 UTC
Source: DER SPIEGEL - International (https://www.spiegel.de/international/index.rss) Fortress Europe: Migrants Abandoned on the Edge of the Sahara Israel-Gaza-Krieg: Menschenrechtler Aryeh Neier über Schuldfrage und Strafverfolgung (Kopie)
Source: NYT > World News (https://rss.nytimes.com/services/xml/rss/nyt/World.xml) Middle East Crisis: Israeli Airstrikes Kill Iranian General in Syria Live Updates: India’s Election Results Suggest a Setback for Modi
Source: BBC News - World (https://feeds.bbci.co.uk/news/world/rss.xml) Shock for India's Modi as opposition set to slash majority Gaza ceasefire plan turns into deadly game of survival
Source: Bitcoin Blockchain (https://blockchain.info/q/latesthash) 000000000000000000014cd79802b29c1dcd7fc6debee1e3968cfc216b59bf16
-----BEGIN PGP SIGNATURE-----
iQIzBAEBCgAdFiEEeY3BEB897EKK3hJNaLi8sMUCOQUFAmZfIwgACgkQaLi8sMUC OQXZYA/9ElVoUy3Um3IXFSwUGO+ctkvKd6idD7RuOBjqZyfadr4emrDrfQKYbCpa Gik4M1H/GWobO/RaDjeSjQtGUmlPn8anhoFzmI6pPz7fBSfg5VGemllyHI2ypPpf cJ1jLrmzpDGxLqPd/R/WsoE8dY9E7q20JgNESAqEYyjmjxqOjx6EnIjBjy8u+xL3 YWBw5BQn/1XbLXw4X7WJNH1cNIIZDgePdIb8Wq6wEDTzFzAvfw5BPhJ2rVaChV9P 6d25htXLy5FU/qvomiy1C+ZskzbZPKGDNgr8lC/MPeNgLi0d/ps2Rgut/CGjKreW UiBmp3xslizR2/WhpRrcz0VLYxdNolfPY0odpgXkvQSEqGiZ1gOw5OQIN0f8HMiL nOXnnxFVgdO/I/x9X2DwKAGwuts/GSeWOHdeNxvflyDGEYJHt9YMT7kXcJ0/dl6z QSNHDoCMzMkxBCX23mlgY8pDSjw0Lqud0HDIChi1DFuNk7m1SfMIKGOn0ZAPsNqX RuMiLCMOPzdE8BBBpKFwZFtx0zyC78xAOBK1M8DqlUexT3CBGFjOwCmGY27dLFZe 6ygdrqptb5uDOXFsw63cWSOilCnEcx7M8FDX7QjuV6EUQwvsxpeKvHZIFVlJNQCX L5F8Lig/y4Q9iCjGiu3oT5zPuuEXPhKkyPsIeM9lC+zP/eC8rL4= =E7lp -----END PGP SIGNATURE----- ```
To view all past canaries, see:
- <https://www.buskill.in/category/Canary/>
What is BusKill?
BusKill is a laptop kill-cord. It's a USB cable with a magnetic breakaway that you attach to your body and connect to your computer.
| [!What is BusKill? (Explainer Video)](https://www.buskill.in/#demo) | |:--:| | Watch the BusKill Explainer Video for more info youtube.com/v/qPwyoD_cQR4 |
If the connection between you to your computer is severed, then your device will lock, shutdown, or shred its encryption keys -- thus keeping your encrypted data safe from thieves that steal your device.
- • 100%samcurry.net Hacking Millions of Modems (and Investigating Who Hacked My Modem)
Two years ago, something very strange happened to me while working from my home network. I was exploiting a blind XXE vulnerability that required an external HTTP server to smuggle out files, so I spun up an AWS box and ran a simple Python webserver to receive the traffic from the vulnerable server.
cross-posted from: https://reddthat.com/post/20097432
> Unbelievable...
- • 87%arstechnica.com Federal agency warns critical Linux vulnerability being actively exploited
Cybersecurity and Infrastructure Security Agency urges affected users to update ASAP.

So I have a situation where I would like to keep data secure. In my mind if I'm working on a computer that has no network connection, this is the safest.
However, I may from time to time need to transfer data to this machine, which introduces a vulnerability. Any thoughts on how I could minimize the risk in this case?
- • 85%theintercept.com This Undisclosed WhatsApp Vulnerability Lets Governments See Who You Message
Engineers warned Meta that nations can monitor chats; staff fear Israel is using this trick to pick assassination targets in Gaza.

- • 66%github.com Recursive clones on case-insensitive filesystems that support symlinks are susceptible to Remote Code Execution
### Impact Repositories with submodules can be crafted in a way that exploits a bug in Git whereby it can be fooled into writing files not into the submodule's worktree but into a `.git/` director...
- • 87%thehackernews.com New Wi-Fi Vulnerability Enables Network Eavesdropping via Downgrade Attacks
New Wi-Fi vulnerability discovered! CVE-2023-52424, dubbed "SSID Confusion attack," affects all operating systems and Wi-Fi clients.

- • 87%arstechnica.com How I upgraded my water heater and discovered how bad smart home security can be
Could you really control someone's hot water with just an email address?

I continue to be amazed that anybody connects their appliances to the internet.
- • 100%www.zone.eu BIMI and DMARC Can't Save You: The Overlooked DKIM Exploit
Analysts at Zone.eu, one of the leading domain registrars and web hosting providers in Europe, have observed a vulnerability affecting the global e-mail ecosystem, stemming from unaddressed warnings in the DomainKeys Identified Mail (DKIM) standard that puts billions of users in risk. This is not an...

- • 95%16years.secvuln.info 16 years of CVE-2008-0166 - Debian OpenSSL Bug
Many DKIM setups used cryptographic keys vulnerable to the 2008 Debian OpenSSL Bug (CVE-2008-0166) in 2024.

Today, 16 years ago, Debian published a security advisory announcing CVE-2008-0166, a severe bug in their OpenSSL package that effectively broke the random number generator and limited the key space to a few ten thousand keys. The vulnerability affected Debian+Ubuntu between 2006 and 2008. In 2007, an email signature system called DKIM was introduced. Is it possible that people configured DKIM in 2007, never changed their key, and are still vulnerable to CVE-2008-0166?
https://mastodon.social/@hanno/112427156548148984
- • 88%arstechnica.com Novel attack against virtually all VPN apps neuters their entire purpose
TunnelVision vulnerability has existed since 2002 and may already be known to attackers.

cross-posted from: https://lemmy.ml/post/15178977
> FWIW, this isn't to do with me personally at all, I'm not looking to do anything dodgy here, but this came up as a theoretical question about remote work and geographical security, and I realised I didn't know enough about this (as an infosec noob) > > Presuming: > * an employer provides the employee with their laptop > * with security software installed that enables snooping and wiping etc and, > * said employer does not want their employee to work remotely from within some undesirable geographical locations > > How hard would it be for the employee to fool their employer and work from an undesirable location? > > I personally figured that it's rather plausible. Use a personal VPN configured on a personal router and then manually switch off wifi, bluetooth and automatic time zone detection. I'd presume latency analysis could be used to some extent?? But also figure two VPNs, where the second one is that provided by/for the employer, would disrupt that enough depending on the geographies involved? > > What else could be done on the laptop itself? Surreptitiously turn on wiki and scan? Can there be secret GPSs? Genuinely curious!
- • 89%lyra.horse Stealing your Telegram account in 10 seconds flat
Say you handed me your phone, what’s the worst I could do in 10 seconds?
- • 77%arstechnica.com Nation-state hackers exploit Cisco firewall 0-days to backdoor government networks
Perimeter devices ought to prevent network hacks. Why are so many devices allowing attacks?

There’s a server, a client, and a hacker in a network. For encryption, the client and the server need to share their private keys. Wouldn’t the hacker be able to grab those during their transmission and decrypt further messages as they please?
- • 100%www.sciencedaily.com Computer scientists unveil novel attacks on cybersecurity
Researchers have found two novel types of attacks that target the conditional branch predictor found in high-end Intel processors, which could be exploited to compromise billions of processors currently in use.

cross-posted from: https://infosec.pub/post/11554206
> Researchers have found two novel types of attacks that target the conditional branch predictor found in high-end Intel processors, which could be exploited to compromise billions of processors currently in use.
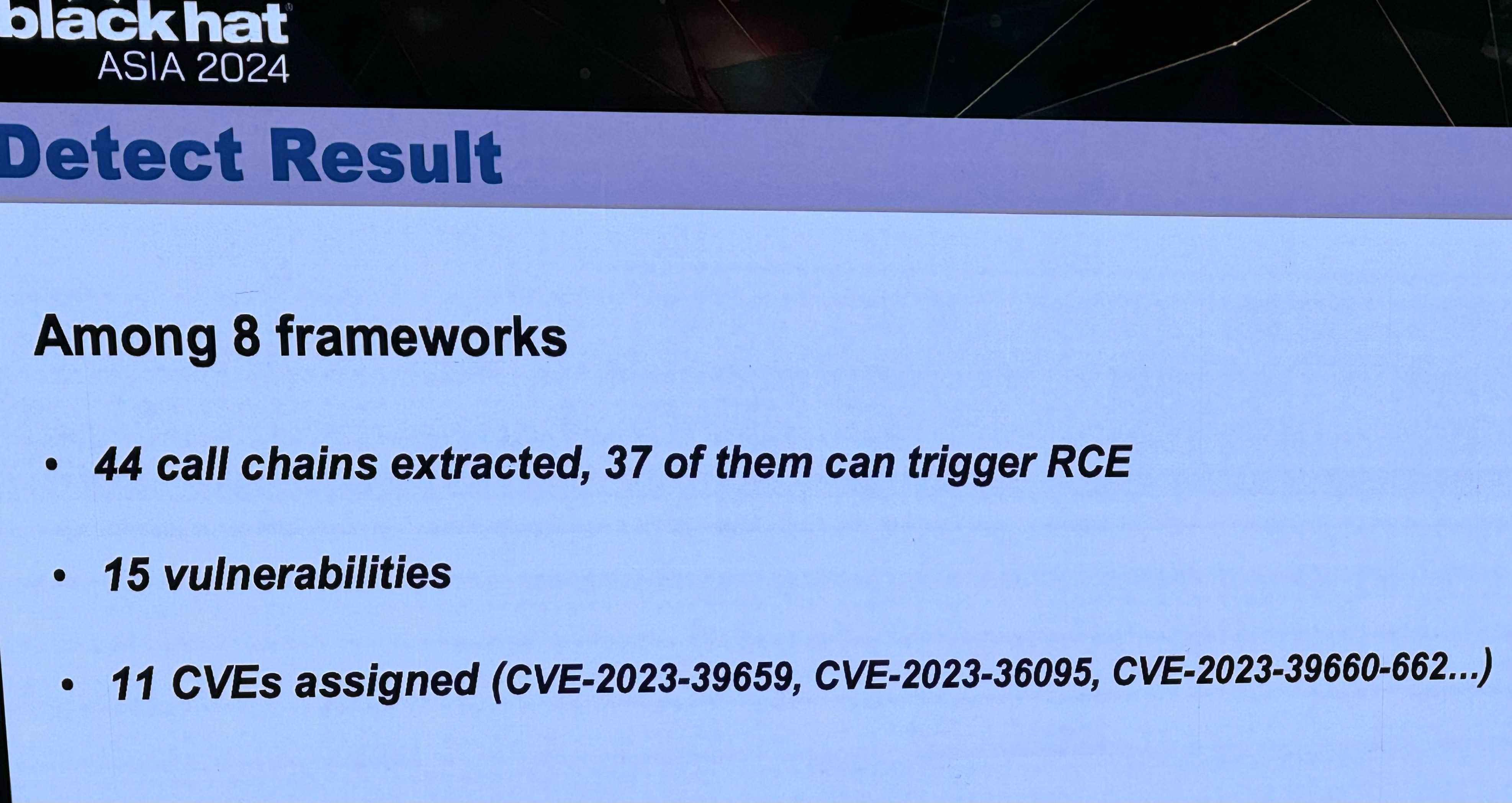
- mastodon.social Kenn White (@kennwhite@mastodon.social)
Attached: 3 images Incredible research at BlackHat Asia today by Tong Liu and team from the Institute of Information Engineering, Chinese Academy of Sciences (在iie.ac.cn 的电子邮件经过验证) A dozen+ RCEs on popular LLM framework libraries like LangChain and LlamaIndex - used in lots of chat-assisted apps i...
- • 100%www.bankinfosecurity.com After XZ Utils, More Open-Source Maintainers Under Attack
Major open-source software projects are warning that more pieces of code than XZ Utils may have been backdoored by attackers, based on ongoing supply-chain attack

cross-posted from: https://infosec.pub/post/11143989
> Fresh Social Engineering Attacks Resemble Tactics Used Against XZ Utils MaintainerMajor open-source software projects are warning that more pieces of code than XZ Utils may have been backdoored by attackers, based on ongoing supply-chain attack attempts that have targeted "popular JavaScript projects," apparently seeking to trick them into sharing code maintainer rights.
- hachyderm.io Simon Tatham (@simontatham@hachyderm.io)
We've released #PuTTY version 0.81. This is a SECURITY UPDATE, fixing a #vulnerability in ECDSA signing for #SSH. If you've used a 521-bit ECDSA key (ecdsa-sha2-nistp521) with any previous version of PuTTY, consider it compromised! Generate a new key pair, and remove the old public key from authori...
We've releasWe've released #PuTTY version 0.81. This is a SECURITY UPDATE, fixing a #vulnerability in ECDSA signing for #SSH.
If you've used a 521-bit ECDSA key (ecdsa-sha2-nistp521) with any previous version of PuTTY, consider it compromised! ed #PuTTY version 0.81. This is a SECURITY UPDATE, fixing a #vulnerability in ECDSA signing for #SSH.
If you've used a 521-bit ECDSA key (ecdsa-sha2-nistp521) with any previous version of PuTTY, consider it compromised!
https://www.chiark.greenend.org.uk/~sgtatham/putty/wishlist/vuln-p521-bias.html
- • 91%www.forbes.com Gmail And YouTube Hackers Bypass Google’s 2FA Account Security
As Gmail and YouTube users take to support forums to complain about accounts being hacked despite having 2FA activated, Google responds with 7-day recovery solution.

- • 100%checkmarx.com New Technique Detected in an Open Source Supply Chain Attack
In a recent attack campaign, cybercriminals were discovered cleverly manipulating GitHub's search functionality, and using meticulously crafted repositories to distribute malware.

- • 94%www.bleepingcomputer.com New Spectre v2 attack impacts Linux systems on Intel CPUs
Researchers have demonstrated the "first native Spectre v2 exploit" for a new speculative execution side-channel flaw that impacts Linux systems running on many modern Intel processors.

cross-posted from: https://infosec.pub/post/10912691
> Researchers have demonstrated the "first native Spectre v2 exploit" for a new speculative execution side-channel flaw that impacts Linux systems running on many modern Intel processors. [...]
- http:// www.flux.utah.edu /paper/singh-nsdi24
https://discuss.systems/@ricci/112247553557306560