Yubikey
- • 100%arstechnica.com YubiKeys are vulnerable to cloning attacks thanks to newly discovered side channel
Sophisticated attack breaks security assurances of the most popular FIDO key.

- • 100%www.yubico.com Eliminating enterprise risk: One phishing-resistant user at a time
Eliminating enterprise risk: One phishing-resistant user at a time

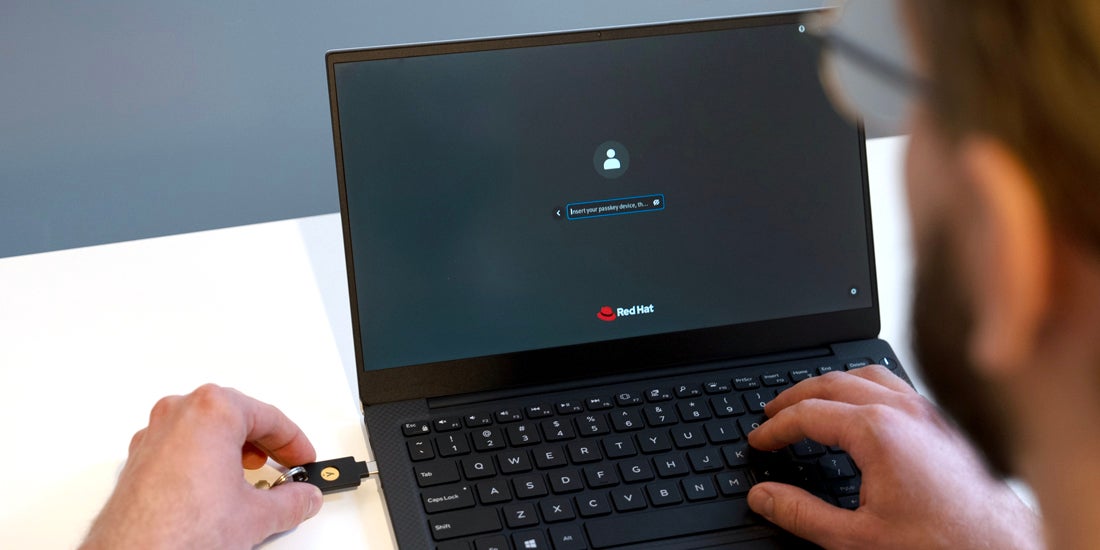
- • 100%www.yubico.com Red Hat Enterprise Linux 9.4 adds passkey support for centrally managed users, including YubiKeys
Red Hat Enterprise Linux 9.4 adds passkey support for centrally managed users, including YubiKeys
- www.yubico.com Empowering enterprise security at scale with new product innovations: YubiKey 5.7 and Yubico Authenticator 7
Empowering enterprise security at scale with new product innovations: YubiKey 5.7 and Yubico Authenticator 7

1 Active user
Next