/c/cybersecurity - Cybersecurity News & Discussion
im aiming to make a chat app secure as theorhetically possible as a webapp. for transparency its open source. id like the experience to be as close to possible to a regular chat app. its important to note; there are limitation with p2p and webapps such that messages cant be sent if the peer isnt connected.
to keep this post brief, please take a look at the readme. it has all the information and links.
i dont think its ready to replace any app or service, but id love to get feedback on what you think would make it so you would use it more than once.
- • 86%www.wired.com Watch How a Hacker’s Infrared Laser Can Spy on Your Laptop’s Keystrokes
Hacker Samy Kamkar is debuting his own open source version of a laser microphone—a spy tool that can invisibly pick up the sounds inside your home through a window, and even the text you’re typing.

Samy Kamkar's latest at Defcon.
Archive link: https://archive.ph/UtTtp
- • 100%h0bbl3s.port0.org Vulnerability scanning with vuls
Table of contents Introduction Summary Considerations Dependencies docker links prereqs vuls Configuration local remote Scan Reports tui vulsrepo Afterword Intro No matter what server OS you run, it can be hard to keep up with what versions of packages you run as well as their vulnerabilities and th...
Just finished up a new post. Hope someone finds it helpful!

Release 1.3.0 (26-07-2024)
Improvements
- Vulnerability Details Page Enhancements: We've significantly enhanced the vulnerabilities details page. It now presents more relevant information and the layout has been substantially improved for a better user experience.
- API Enhancements: Various improvements have been made to the API for better performance and functionality.
- UI Enhancements: Edition/action buttons are now hidden when not logged in (#57).
- Importer Improvements: Enhancements have been made to various importers (37d3a6d).
Fixes
- Custom Vulnerability Display Bug: Fixed an issue where custom vulnerabilities were not displayed correctly (#58).
- New Vulnerability Creation Issue: Resolved the problem where new vulnerabilities couldn't be created without a CVE number (#56).
- Webservice Sorting Fix: Fixed the sorting issue of contributors versus users (46195d1).
- Minor Fixes: Various minor fixes have been implemented to improve overall stability and performance.
!Screenshot_20240726_141051 !Screenshot_20240726_141112
And do not hesitate to create an account to contribute and share your thoughts on the security advisories: https://vulnerability.circl.lu
Funding
The NGSOTI project is dedicated to training the next generation of Security Operation Center (SOC) operators, focusing on the human aspect of cybersecurity. It underscores the significance of providing SOC operators with the necessary skills and open-source tools to address challenges such as detection engineering, incident response, and threat intelligence analysis. Involving key partners such as CIRCL, Restena, Tenzir, and the University of Luxembourg, the project aims to establish a real operational infrastructure for practical training. This initiative integrates academic curricula with industry insights, offering hands-on experience in cyber ranges.
vulnerability-lookup is co-funded by CIRCL and by the European Union. Views and opinions expressed are however those of the author(s) only and do not necessarily reflect those of the European Union or ECCC. Neither the European Union nor the granting authority can be held responsible for them.
> Media coverage largely sucked > > When I just looked at my phone, the headlines were about an unfolding Microsoft global IT outage. My first thought, ransomware. So I logged in and started looking around at what was happening — I’m a CrowdStrike customer — and quickly realised two different, separate things had happened: > > - Microsoft Azure had an outage earlier in the day. This was resolved before I got up. Azure has frequent outages (don’t kill me, Microsoft) — this isn’t abnormal. > - CrowdStrike had made a boo-boo and pushed out a channel update that had borked a decent percentage of customers. > > The media connected these two events together and conflated them. They weren’t connected.
- www.buskill.in BusKill goes to DEF CON 32 - BusKill
Join BusKill at DEF CON 32 for our presentation titled "Open Hardware Design for BusKill Cord" in the Demo Lab

We're happy to announce that BusKill is presenting at DEF CON 32.
What: Open Hardware Design for BusKill Cord When: 2024-08-10 12:00 - 13:45 Where: W303 – Third Floor – LVCC West Hall
| [!BusKill goes to DEF CON 32 (Engage)](https://www.buskill.in/defcon32/) | |:--:| | BusKill is presenting at DEF CON 32 |
What is BusKill?
BusKill is a laptop kill-cord. It's a USB cable with a magnetic breakaway that you attach to your body and connect to your computer.
| [!What is BusKill? (Explainer Video)](https://www.buskill.in/#demo) | |:--:| | Watch the BusKill Explainer Video for more info youtube.com/v/qPwyoD_cQR4 |
If the connection between you to your computer is severed, then your device will lock, shutdown, or shred its encryption keys -- thus keeping your encrypted data safe from thieves that steal your device.
What is DEF CON?
DEF CON is a yearly hacker conference in Las Vegas, USA.
| [!DEF CON Documentary](https://www.buskill.in/defcon32/) | |:--:| | Watch the DEF CON Documentary for more info youtube.com/watch?v=3ctQOmjQyYg |
What is BusKill presenting at DEF CON?
I (goldfishlaser) will be presenting Open Hardware Design for BusKill Cord in a Demo Lab at DEF CON 32.
What: Open Hardware Design for BusKill Cord When: Sat Aug 10 12PM – 1:45PM Where: W303 – Third Floor – LVCC West Hall
Who: Melanie Allen (goldfishlaser) More info
Talk Description
BusKill is a Dead Man Switch triggered when a magnetic breakaway is tripped, severing a USB connection. I’ve written OpenSCAD code that creates a 3D printable file for plastic parts needed to create the magnetic breakaway. Should anyone need to adjust this design for variations of components, the code is parameterized allowing for easy customization. To assemble a BusKill Dead Man Switch cord you will need:
- a usb-a extension cord,
- a usb hard drive capable of being attached to a carabiner,
- a carabiner,
- the plastic pieces in this file,
- a usb female port,
- a usb male,
- 4 magnets,
- 4 pogo pins,
- 4 pogo receptors,
- wire,
- 8 screws,
- and BusKill software.
| [!Image of the Golden BusKill decoupler with the case off](https://www.buskill.in/defcon32/) | |:--:| | Golden DIY BusKill Print |
Full BOM, glossary, and assembly instructions are included in the github repository. The room holds approx. 70 attendees seated. I’ll be delivering 3 x 30 min presentations – with some tailoring to what sort of audience I get each time.
Meet Me @ DEF CON
If you'd like to find me and chat, I'm also planning to attend:
- ATL Meetup (DCG Atlanta Friday: 16:00 – 19:00 \| 236),
- Hacker Kareoke (Friday and Sat 20:00-21:00 \| 222),
- Goth Night (Friday: 21:00 – 02:00 \| 322-324),
- QueerCon Mixer (Saturday: 16:00-18:00 \| Chillout 2),
- EFF Trivia (Saturday: 17:30-21:30 \| 307-308), and
- Jack Rysider’s Masquerade (Saturday: 21:00 – 01:00 \| 325-327)
I hope to print many fun trinkets for my new friends, including some BusKill keychains.
| [!Image shows a collection of 3D-printed bottle openers and whistles that say "BusKill"](https://www.buskill.in/defcon32/) | |:--:| | Come to my presentation @ DEF CON for some free BusKill swag |
By attending DEF CON, I hope to make connections and find collaborators. I hope during the demo labs to find people who will bring fresh ideas to the project to make it more effective.
- github.com GitHub - cve-search/vulnerability-lookup: Vulnerability Lookup facilitates quick correlation of vulnerabilities from various sources, independent of vulnerability IDs, and streamlines the management of Coordinated Vulnerability Disclosure (CVD).
Vulnerability Lookup facilitates quick correlation of vulnerabilities from various sources, independent of vulnerability IDs, and streamlines the management of Coordinated Vulnerability Disclosure ...
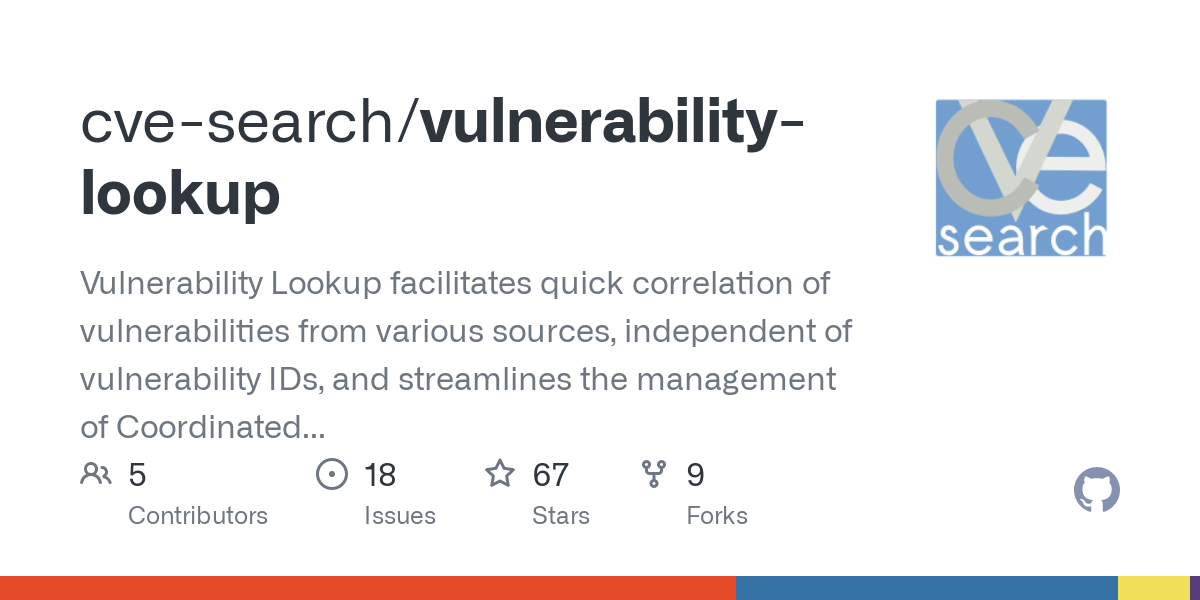
Vulnerability Lookup facilitates quick correlation of vulnerabilities from various sources (NIST, GitHub, CSAF-Siemens, CSAF-CISCO, CSAF-CERT-Bund, PySec, VARIoT, etc.), independent of vulnerability IDs, and streamlines the management of Coordinated Vulnerability Disclosure (CVD). Vulnerability Lookup is also a collaborative platform where users can comment on security advisories and create bundles.
A Vulnerability Lookup instance operated by CIRCL is available at https://vulnerability.circl.lu.
- blog.cloudflare.com Automatically replacing polyfill.io links with Cloudflare’s mirror for a safer Internet
polyfill.io, a popular JavaScript library service, can no longer be trusted and should be removed from websites

cross-posted from: https://programming.dev/post/16106778 >> Contrary to what is stated on the polyfill.io website, Cloudflare has never recommended the polyfill.io service or authorized their use of Cloudflare’s name on their website. We have asked them to remove the false statement, and they have, so far, ignored our requests. This is yet another warning sign that they cannot be trusted.
- https:// www.wsj.com /articles/paypal-is-planning-an-ad-business-using-data-on-its-millions-of-shoppers-cc5e0625
Wall Street Journal (paywalled) The digital payments company plans to build an ad sales business around the reams of data it generates from tracking the purchases as well as the broader spending behaviors of millions of consumers who use its services, which include the more socially-enabled Venmo app.
PayPal has hired Mark Grether, who formerly led Uber’s advertising business, to lead the effort as senior vice president and general manager of its newly-created PayPal Ads division.
Not sure if there’s a better community to ask this, but I’m trying to find a good quality non-cloud-based IP camera that I can feed into a standardized video recording software over a network. Ideally, it would be Wi-Fi capable as well.
Everywhere I’ve looked, they all reach out to a third-party and go through an app or are through junction box and are analog-based.
Does anyone know if an option like this exists?
- • 50%heise.de Angeblicher Tesla-Hack mit Flipper Zero entpuppt sich als Sturm im Wasserglas
Mittels eines gefälschten Gast-WLANs im Tesla-Design könnten Angreifer an Superchargern oder in Service-Centern Zugänge abgreifen, warnen die Experten.

Und mal wieder: Es ist nur ein Werkzeug, mit dem halt mit genug krimineller Energie auch Blödsinn gemacht wird. In dem Fall war es auch nicht mal ein Angriff auf das Auto, der “spezielle Hardware “ benötigen würde.
- www.theregister.com JetBrains TeamCity under attack by ransomware thugs
More than 1,000 servers remain unpatched and vulnerable

So, yeah. Other than stated, Spotify does not provide 2FA (shame on them!), so I use a strong password and since years nothing happened.
This early morning I got multiple mails that my account was logged in from Brazil, from the USA, from India, and some other countries. There were songs liked and playlists created so it wasn’t a malicious e-mail but some people actually were able to log on to my Spotify account.
I of course changed the password and logged out all accounts and checked allowed apps, etc. and everything looks fine.
But I wonder … was there something that happened recently? The common sites to check such things do not list my old Spotify password, and a quick web research does not bring anything up.
Any clue what could have happened here?
Infomaniak claims to use TLS, but
> The first link in the TLS chain is executed via a purely internal network by the webmail and Smtp servers and is not available in TLS for performance reasons.
is this normal, acceptable, irrelevant, standard, a red flag?
they are the biggest hosting provider of Switzerland, so I somehow have a hard time believing, they lack resources to implement TLS right.
- http:// archive.today /1W8V9
The reporting methodology employed should yield valuable insights, spanning both technical details and high-level strategic considerations.
I wrote about my perception of what risks AI brings to society in 2024. And it's not all about cybersecurity 😉
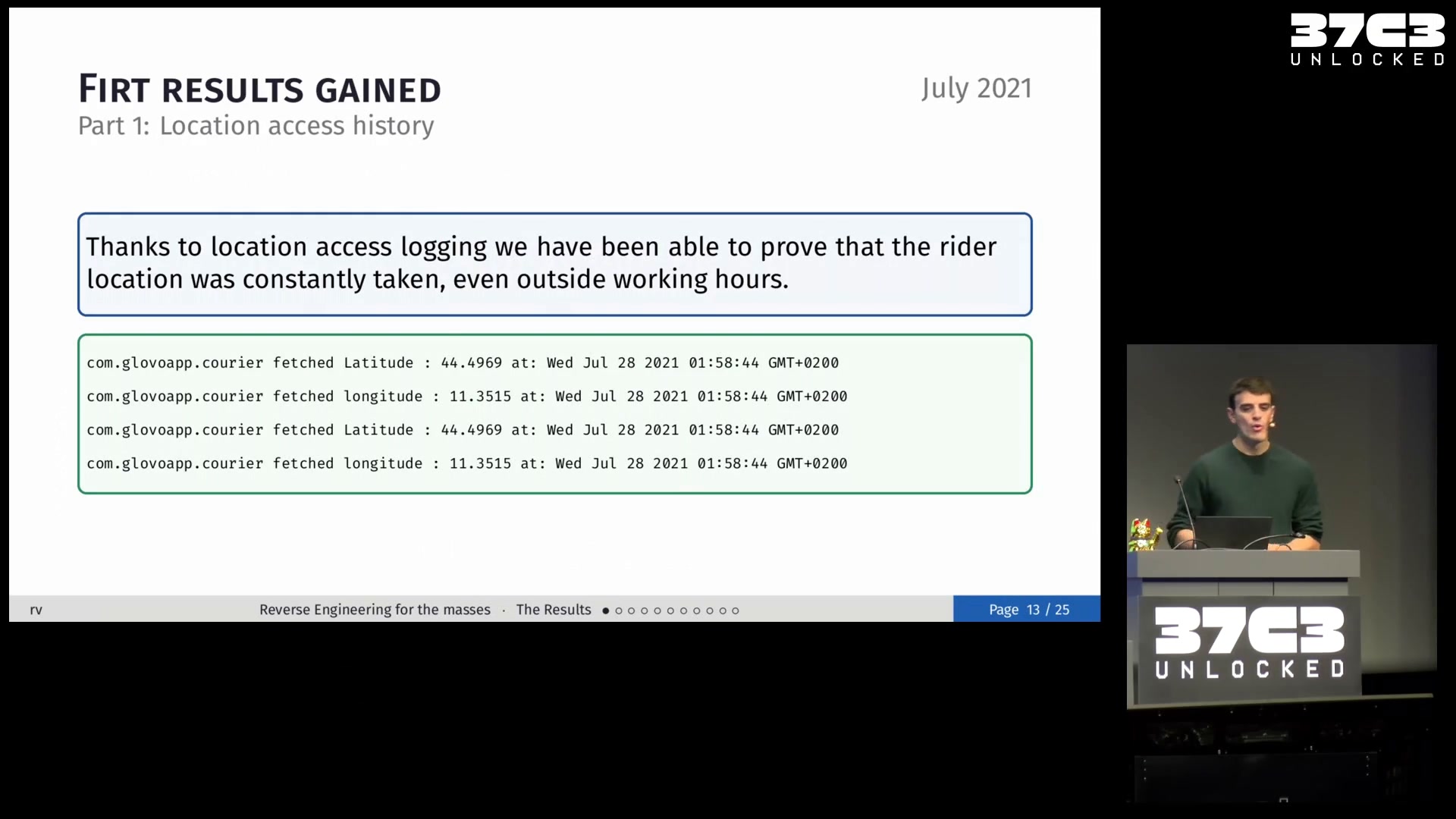
- • 92%media.ccc.de Mobile reverse engineering to empower the gig economy workers and labor unions
[Reversing.works](https://reversing.works) will outline five years of experience linking trade unions, gig economy workers, GDPR and mobi...
- www.ultra-unlimited.com 2024 Weaponized AI Arms Race: Impacts and Ethical Stakes — Ultra Unlimited
In this deep dive article learn more about the 2024 Weaponized AI Arms Race and the societal impacts and ethical stakes of systems like OpenAI's Q*.

- • 96%arstechnica.com Just about every Windows and Linux device vulnerable to new LogoFAIL firmware attack
UEFIs booting Windows and Linux devices can be hacked by malicious logo images.

- • 100%www.bleepingcomputer.com Mozilla patches Firefox, Thunderbird against zero-day exploited in attacks
Mozilla released emergency security updates today to fix a critical zero-day vulnerability exploited in the wild, impacting its Firefox web browser and Thunderbird email client.

- • 100%blog.solidsnail.com From Terminal Output to Arbitrary Remote Code Execution
It was the year of the Linux desktop 1978. Old yellowed computers were not yet old, nor yellowed. Digital Equipment Corporation released the first popular terminal to support a standardized in-band encoding for control functions, the VT100.
cross-posted from: https://infosec.pub/post/2466014
> This is my first write-up, on a vulnerability I discovered in iTerm2 (RCE). Would love to hear opinions on this. I tried to make the writing engaging.
I only wonder because, while I know no one could advise per se that people deliberately make bad security decisions, I don't feel as a layman that the nature of the risk is adequately explained.
Specifically, if you use a really old OS or an old now unsupported phone. The explanations for why this is dangerous tend to focus on the mechanism by which it creates a security flaw (lack of patches, known hardware security flaws that can never be patched).
If we use an analogy of physical security whereby the goal is to prevent physical intrusion by thieves or various malicious actors, there's a gradient of risk that's going to depend a bit on things like who and where you are. If you live in a remote cabin in the woods and left your door open, that's bad, but probably less bad than in a high crime area in a dense city. Similarly, if you're a person of note or your house conspicuously demonstrates wealth, security would be more important than if it you're not and it doesn't.
I would think, where human beings are making conscious choices about targets for cybercrime some parralells would exist. If then, you turn on an old device that's long obsolete for the first time in years and connect to the internet with it, while I know you are theoretically at great risk because your doors and windows are essentially wide open, how risky is that exactly? If you just connect, at home on your wifi and don't do anything? Is someone inevitably going to immediately find and connect to this device and exploit it's vulnerabilities? Or does there have to be a degree of bad luck involved?
I've brought up the idea of malicious actors who are human beings making conscious decisions, (hackers), but I was once told the concern is more to do with automated means of finding such devices when they're exposed to the internet. This makes more sense since a theoretical hacker doesn't have to sit around all day just hoping someone in the world will use an outdated device and that they'll somehow see this activity and be able to exploit the situation, but I guess, it seems hard for me to imagine that such bots or automated means of scanning, even if running all day will somehow become aware the minute anyone, anywhere with an insecure device connects to the internet. Surely there has to be some degree coincidental happenstance where a bot is directed to scan for connections to a particular server, like a fake website posing as a bank or something? It just doesn't seem it could be practical otherwise.
If I'm at all accurate in my assumptions, it sounds then like there's a degree to which a random person, not well known enough to be a specific target, not running a website or online presence connecting an insecure device to the internet, while engaging in some risk for sure, isn't immediately going to suffer consequences without some sort of inciting incident. Like falling for a phishing scam, or a person specifically aware of them with mal intent trying to target them in particular. Is that right?
I know this may be a very general question, but there are so many resources I don't know where to start.
I'm afraid with the free TryHackMe plan I'm limiting myself a lot.
I know portswigger trining, is it better than TryHackMe?
Am I better off starting directly with CTFs? If yes, which is the best to use? (overthewire, hackthebox ...)
Is roadmap.sh reliable?
How important are the certificates? I am a tech illiterate but never cared about certificates.
Or as a last resort, is it better to start directly with hackthebox?
- www.gosecure.net How Unparalleled RDP Monitoring Reveal Attackers’ Tradecraft - GoSecure
Luring threat actors into RDP traps reveals attackers' tactics. This blog summarizes an hour-long presentation about what can be found in those traps.

Researchers analyzed 190 million hacking events on a honeynet and categorized the types of hackers into Dungeons and Dragons classses.
Rangers evaluate the system and set conditions for a follow-on attack.
Thieves install cryptominers and other profiteering software.
Barbarians attempt to brute force their way into adjacent systems.
Wizards connect the newly compromised system to a previous to establish 'portals' to tunnel through to obscure their identity.
Bards have no apparent hacking skill and likely purchase or otherwise acquired access. They perform basic computer tasks.
OK, first of all, I'm no expert, I have some training in networking and very little in cyber security. I live in a small community and there's is an ISP providing service to the whole community. Today I got an old ip camera and tried to hook it up, I couldn't figure out it's ip address and scanned my network (let's say 10.0.0.0/24) for ip addresses and it still wouldn't show up, so I scanned what I know was it's last subnet, let's say 10.0.10.0/24 and found out there as a host at every address, one was even an HP printer from a family the other side of the community which I was able to gain access simply by going to it's address. When I go to my router's web ui I can see that it's gateway is 10.0.8.1 and a 255.255.252.0 subnet. So my question is, is this all normal? Or should I contact someone about it?
- www.humblebundle.com CyberSecurity: Zero to Hero
We’ve teamed up with Packt for our newest bundle. Get cybersecurity training courses to learn coding, testing, and more. Pay what you want & support World Wildlife Fund!

geteilt von: https://feddit.de/post/1475295
> Bundle Description: > > Become a cybersecurity champion > > > Want to train up to take on today’s biggest cybersecurity challenges? Go from zero to hero with this comprehensive bundle of courses from Packt. Focus on the fundamentals, and build up advanced skills through hands-on training. Learn how to write secure code, test your systems’ defenses, how to be an ethical hacker, and more—and help support World Wildlife Fund with your purchase! > > Pay at least €1 for 4 items, > Pay more than the average for 9 items, > Pay at least €22.75 for 22 items > > > Does anyone has experience with Packt's courses? Anything good in there?
- • 100%arstechnica.com Torrent of image-based phishing emails are harder to detect and more convincing
The arms race between scammers and defenders continues.

Phishing mongers have released a torrent of image-based junk emails that embed QR codes into their bodies to successfully bypass security protections and provide a level of customization to more easily fool recipients, researchers said.
In many cases, the emails come from a compromised email address inside the organization the recipient works in, a tactic that provides a false sense of authenticity, researchers from security firm Inky said. The emails Inky detected instruct the employee to resolve security issues such as a missing two-factor authentication enrollment or to change a password and warn of repercussions that may occur if the recipient fails to follow through. Those who take the bait and click on the QR code are led to a site masquerading as a legitimate one used by the company but it captures passwords and sends them to the attackers.
Inky described the campaign's approach as “spray and pray” because the threat actors behind it send the emails to as many people as possible to generate results.
There are a few things that make this campaign stand out. First, the emails contain no text. Instead, they have only an attached image file. This allows the emails to escape notice by security protections that analyze the text-based words sent in an email. Some email programs and services, by default, automatically display attached images directly in the body, with some providing no way to suppress them. Recipients then often don’t notice that the image-based email contains no text.
Another distinguishing feature: the images embed a QR code that leads to the credential-harvesting site. This can reduce the time it takes to visit the site and lower the chance the employee will realize something is amiss. The QR codes also cause the loaded website to prefill the recipient's unique email address in the username field. This adds another false sense of assurance that the email and site are legitimate.
In a writeup published Friday, the Inky researchers wrote:
It’s important to note that these three QR Code phishing emails weren’t sent to just a handful of INKY customers. They were part of a “spray and pray” approach. Phishers send their emails to as many people as possible (spray) and then hope (pray) that a strong majority of recipients will fall for the ruse. In this case, multiple industries were attacked. Of the 545 emails noted thus far, intended victims were in the US and Australia. They included nonprofits, multiple wealth management firms, management consultants, a land surveyor, flooring company, and more.
It has long been possible—not to mention a good practice—for privacy-minded people to configure email settings to block the loading of images stored remotely. Scammers and snoops use external images to determine if a message they sent has been opened since the recipient’s device makes a connection to a server hosting the image. Gmail and Thunderbird don't display attached images in the body, but Inky said other clients or services do. People using such clients or services should turn off this feature if possible.
Unfortunately, it's more problematic to block images that are embedded into an email. I couldn't find a setting in Gmail to suppress the loading of embedded images. Thunderbird prevents embedded images from being displayed, but it requires reading the entire message plaintext mode. That, in turn, breaks helpful formatting.
All of this leaves users with the same countermeasures that have been failing them for decades now. They include:
It’s easy for people to dismiss phishing attacks as unsophisticated and perpetuate the myth that only inattentive people fall for them. In fact, studies and anecdotal evidence suggest that phishing is among the most effective and cost-effective means for carrying out network intrusions. With 3.4 billion spam emails sent every day, according to AGG IT Services, and one in four people reporting they have clicked on a phishing email at work, according to Tessian, people underestimate the costs of phishing at their own peril.
- www.barmer.de Hackerangriff auf externen BARMER-Dienstleister – Mögliches Schadensausmaß wird geprüft | BARMER
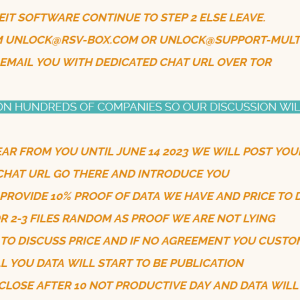
Ein Dienstleister der BARMER ist Ziel eines Hackerangriffs geworden. Dieser Dienstleister unterstützt die Kasse bei der Umsetzung ihres Bonusprogramms. Aktuell laufen Prüfungen, ob bei diesem Angriff, der am 31. Mai 2023 stattfand, auch Zugriff auf BARMER-Daten erfolgt ist.

Original URL: https://www.barmer.de/presse/presseinformationen/pressearchiv/hackerangriff-auf-externen-barmer-dienstleister-1231230
--- Hackerangriff auf externen BARMER-Dienstleister – Mögliches Schadensausmaß wird geprüft
Berlin, 17. Juni 2023 – Ein Dienstleister der BARMER ist Ziel eines Hackerangriffs geworden. Dieser Dienstleister unterstützt die Kasse bei der Umsetzung ihres Bonusprogramms. Aktuell laufen Prüfungen, ob bei diesem Angriff, der am 31. Mai 2023 stattfand, auch Zugriff auf BARMER-Daten erfolgt ist. Die entsprechende Sicherheitslücke wurde vom Dienstleister geschlossen. Der Angriff erfolgte ausschließlich auf den Dienstleister der Kasse. Eine Verbindung zur BARMER-IT-Umgebung bestand zu keinem Zeitpunkt. Vorsorglich wurden relevante Behörden über diesen Vorfall in Kenntnis gesetzt.
Für Rückfragen wenden Sie sich an Unternehmenssprecher Athanasios Drougias unter: 0170 7614752 bzw. athanasios.drougias@barmer.de
Presseabteilung der BARMER Athanasios Drougias (Leitung), Telefon 0800 33 30 04 99-1421 bzw. 0170 7614752 E-Mail: athanasios.drougias@barmer.de
- www.bleepingcomputer.com Reddit hackers threaten to leak data stolen in February breach
The BlackCat (ALPHV) ransomware gang is behind a February cyberattack on Reddit, where the threat actors claim to have stolen 80GB of data from the company.

- • 100%www.bleepingcomputer.com Microsoft’s Azure portal down following new claims of DDoS attacks
The Microsoft Azure Portal is down on the web as a threat actor known as Anonymous Suda claims to be targeting the site with a DDoS attack.

- www.keytos.io Microsoft Azure Vulnerability Still Affecting Thousands of New Subdomains Each Month
Subdomain takeover is a vulnerability that has plagued cloud users for years. Keytos Researches uncover an easy way to find thousands of new vulnerable domains each month.
I feel like I'm missing a step. You take down your website, but leave the DNS entry and the attacker does what? Builds a site that has the IP address your CNAME is pointing to? Can anyone make a website in azure and pick the IP address they want? Thanks
- mastodon.social Ars Technica (@arstechnica@mastodon.social)
Attached: 1 image Millions of Americans’ personal DMV data exposed in massive MOVEit hack Over 6.5 million residents of two states affected, impact may potentially widen. https://arstechnica.com/information-technology/2023/06/millions-of-americans-personal-dmv-data-exposed-in-massive-moveit-hack/...
- www.theguardian.com US mother gets call from ‘kidnapped daughter’ – but it’s really an AI scam
Jennifer DeStefano tells US Senate about dangers of artificial technology after receiving phone call from scammers sounding exactly like her daughter

After being scammed into thinking her daughter was kidnapped, an Arizona woman testified in the US Senate about the dangers side of artificial intelligence technology when in the hands of criminals.
Jennifer DeStefano told the Senate judiciary committee about the fear she felt when she received an ominous phone call on a Friday last April.
Thinking the unknown number was a doctor’s office, she answered the phone just before 5pm on the final ring. On the other end of the line was her 15-year-old daughter – or at least what sounded exactly like her daughter’s voice.
“On the other end was our daughter Briana sobbing and crying saying ‘Mom’.”
Briana was on a ski trip when the incident took place so DeStefano assumed she injured herself and was calling let her know.
DeStefano heard the voice of her daughter and recreated the interaction for her audience: “‘Mom, I messed up’ with more crying and sobbing. Not thinking twice, I asked her again, ‘OK, what happened?’”
She continued: “Suddenly a man’s voice barked at her to ‘lay down and put your head back’.”
Panic immediately set in and DeStefano said she then demanded to know what was happening.
“Nothing could have prepared me for her response,” Defano said.
Defano said she heard her daughter say: “‘Mom these bad men have me. Help me! Help me!’ She begged and pleaded as the phone was taken from her.”
“Listen here, I have your daughter. You tell anyone, you call the cops, I am going to pump her stomach so full of drugs,” a man on the line then said to DeStefano.
The man then told DeStefano he “would have his way” with her daughter and drop her off in Mexico, and that she’d never see her again.
At the time of the phone call, DeStefano was at her other daughter Aubrey’s dance rehearsal. She put the phone on mute and screamed for help, which captured the attention of nearby parents who called 911 for her.
DeStefano negotiated with the fake kidnappers until police arrived. At first, they set the ransom at $1m and then lowered it to $50,000 when DeStefano told them such a high price was impossible.
She asked for a routing number and wiring instructions but the man refused that method because it could be “traced” and demanded cash instead.
DeStefano said she was told that she would be picked up in a white van with bag over her head so that she wouldn’t know where she was going.
She said he told her: “If I didn’t have all the money, then we were both going to be dead.”
But another parent with her informed her police were aware of AI scams like these. DeStefano then made contact with her actual daughter and husband, who confirmed repeatedly that they were fine.
“At that point, I hung up and collapsed to the floor in tears of relief,” DeStefano said.
When DeStefano tried to file a police report after the ordeal, she was dismissed and told this was a “prank call”.
A survey by McAfee, a computer security software company, found that 70% of people said they weren’t confident they could tell the difference between a cloned voice and the real thing. McAfee also said it takes only three seconds of audio to replicate a person’s voice.
DeStefano urged lawmakers to act in order prevent scams like these from hurting other people.
She said: “If left uncontrolled, unregulated, and we are left unprotected without consequence, it will rewrite our understanding and perception what is and what is not truth. It will erode our sense of ‘familiar’ as it corrodes our confidence in what is real and what is not.”
- • 100%www.cnbc.com U.S. government says several agencies hacked as part of broader cyberattack
Jen Easterly, head of the top civilian cybersecurity watchdog, said the agency was tracking the hackers “as a well-known ransomware group.”
- • 100%www.bleepingcomputer.com Barracuda says hacked ESG appliances must be replaced immediately
Email and network security company Barracuda warns customers they must replace Email Security Gateway (ESG) appliances hacked in attacks targeting a now-patched zero-day vulnerability.
This news is “stunning” say many cybersecurity experts; it’s so bad that a patch can’t resolve it, companies have to completely stop using these (very expensive) machines and get new ones.
- • 100%securityaffairs.com Clop ransomware gang claims the hack of hundreds of victims
Clop ransomware group claims to have hacked hundreds of companies globally by exploiting MOVEit Transfer vulnerability
Clop seems to be on a roll, first with GoAnywhere and now with Moveit
- • 100%www.csoonline.com ChatGPT creates mutating malware that evades detection by EDR
Mutating, or polymorphic, malware can be built using the ChatGPT API at runtime to effect advanced attacks that can evade endpoint detections and response (EDR) applications.

- seirim.com SEIRIM
Sharp, fast, cybersecure and conversion-focused websites. Specialties: Corporate Sites - Cybersecurity - SEO - Web Apps - E-Commerce in Shanghai
An overview of the main areas companies need to pay attention to and the tools they can use to get their cybersecurity in better shape.

